FAQs
Complete the form below to get started.





.avif)
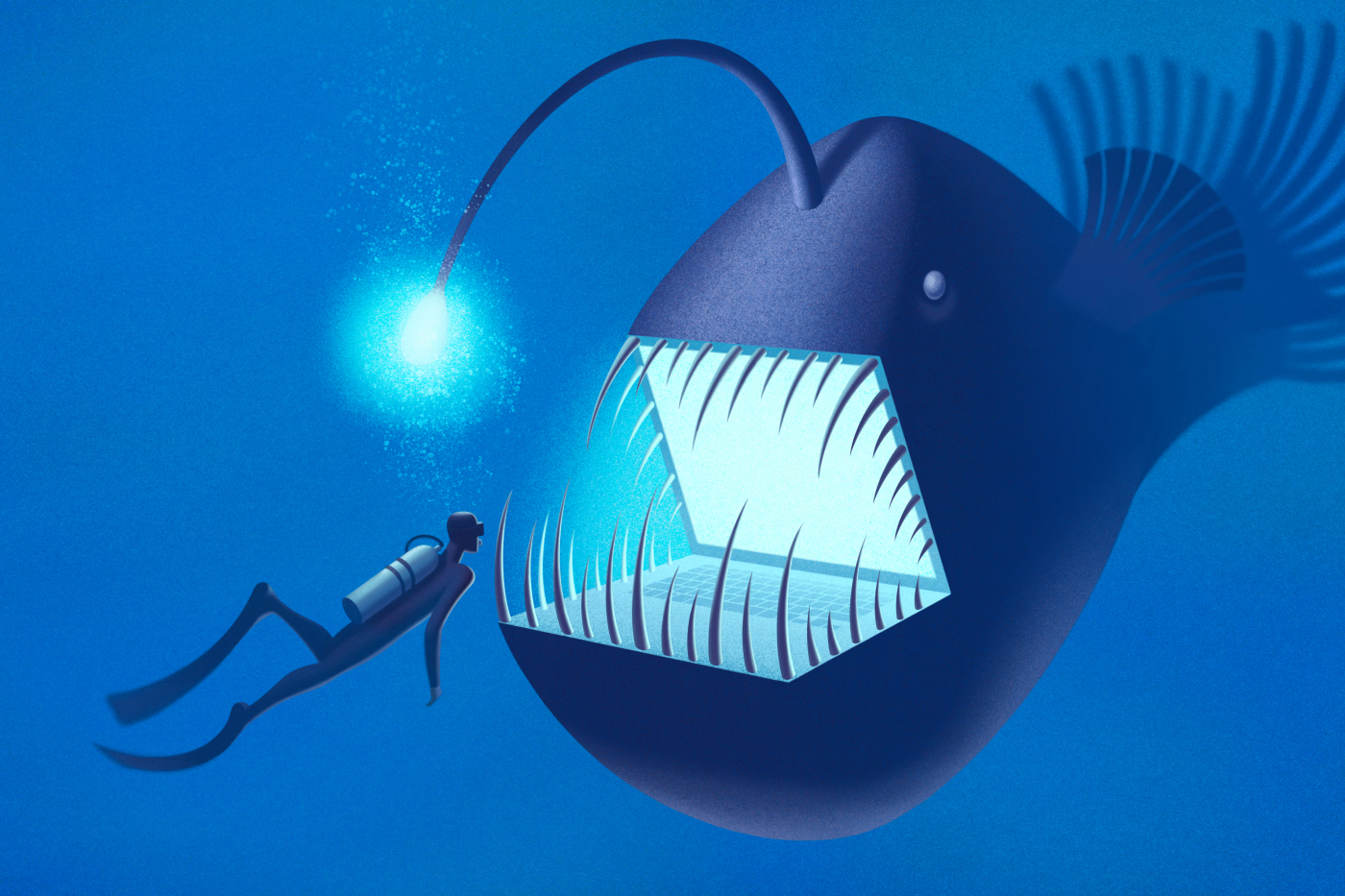
Making Cyber Risk Board Ready: Strategies for Winning Boardroom Confidence
Winning board confidence on cyber risk requires more than technical reporting. Security leaders need to support better governance decisions and communicate exposure in a way directors can act on.
Blog
Never Miss a Human Risk Insights
Subscribe to the Dune Risk Brief - weekly trends, threat models,
and strategies for enterprise CISOs.
and strategies for enterprise CISOs.
Oops! Something went wrong while submitting the form.