Expose, Score, & Reduce User Risk
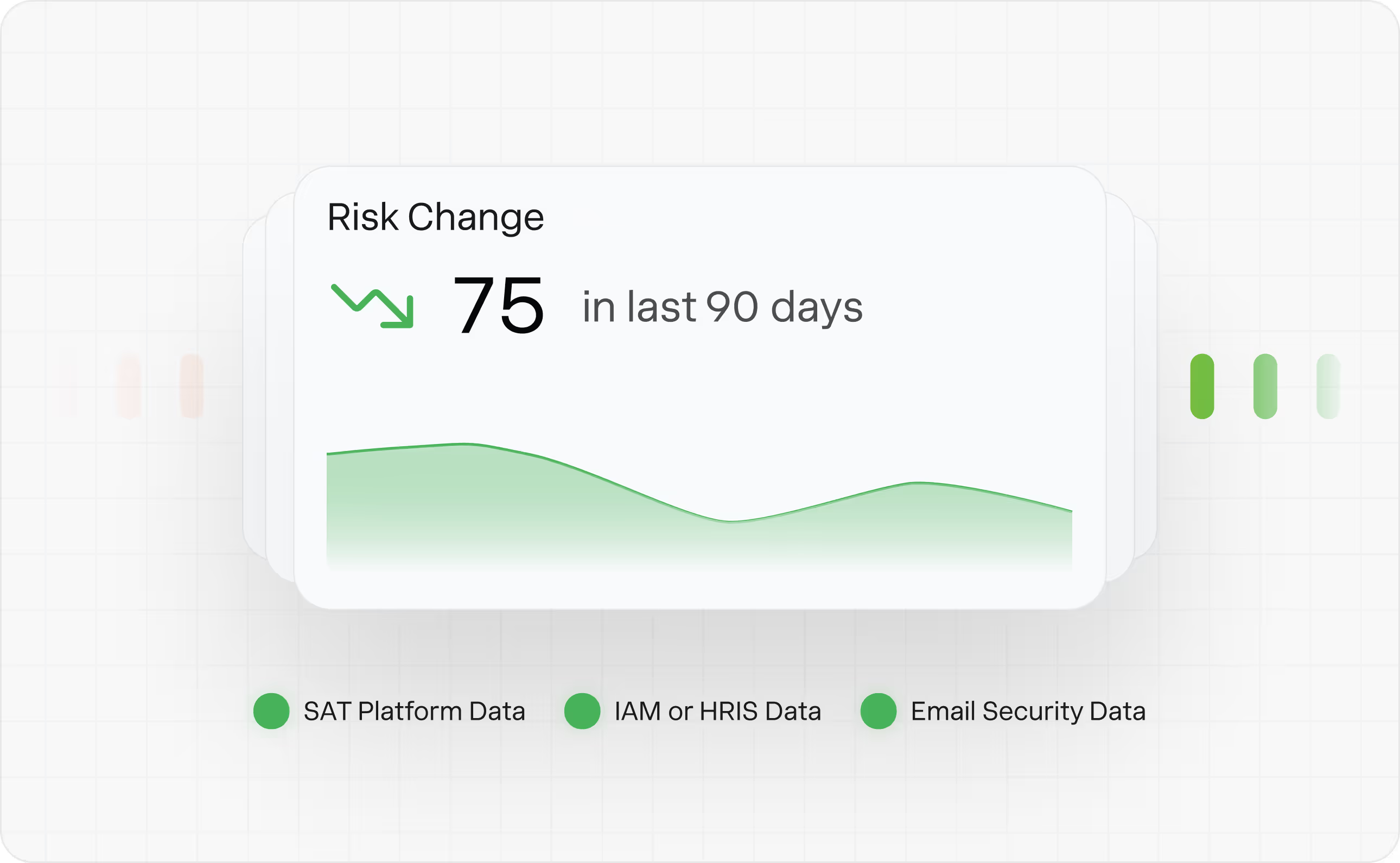
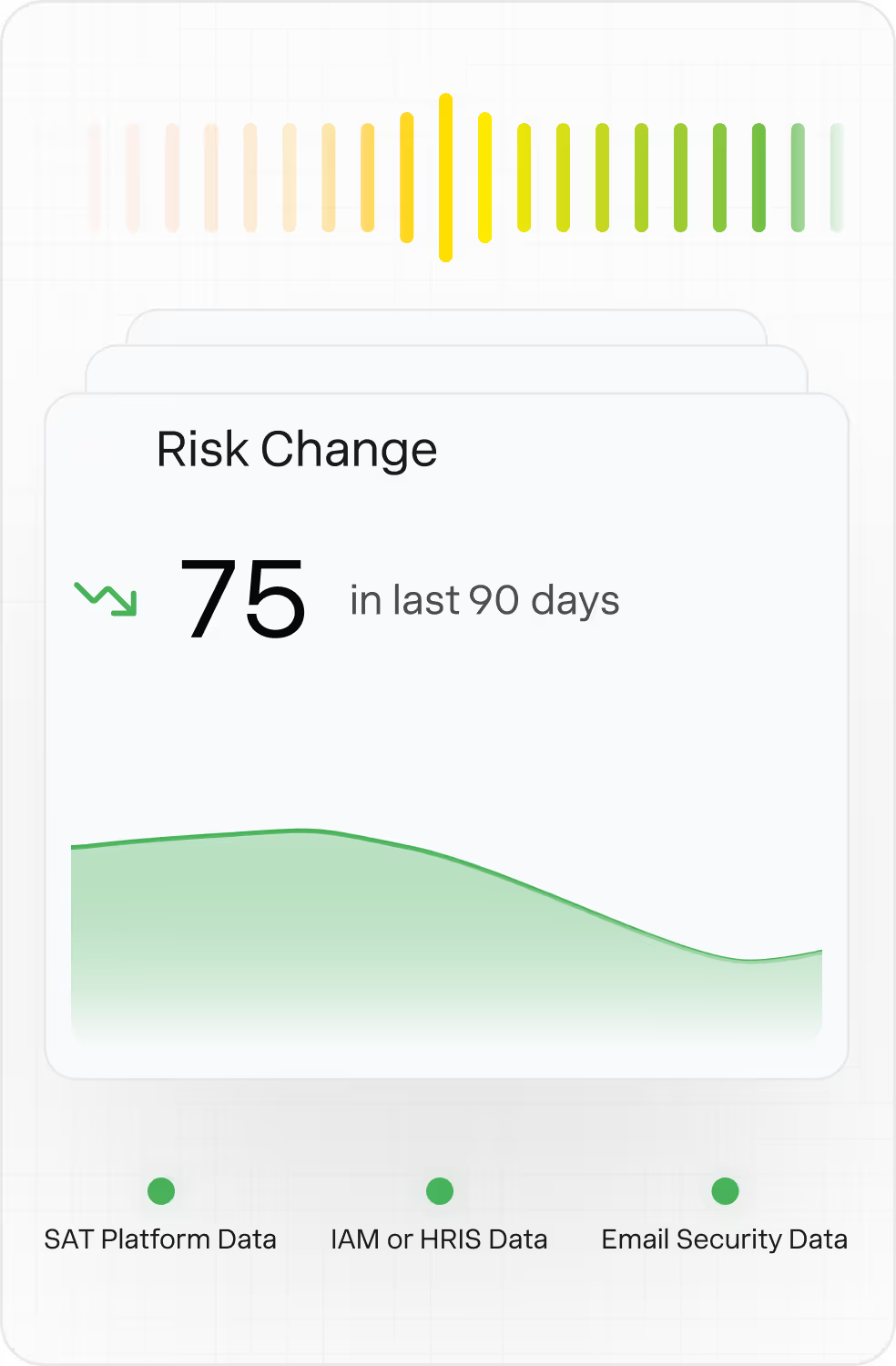
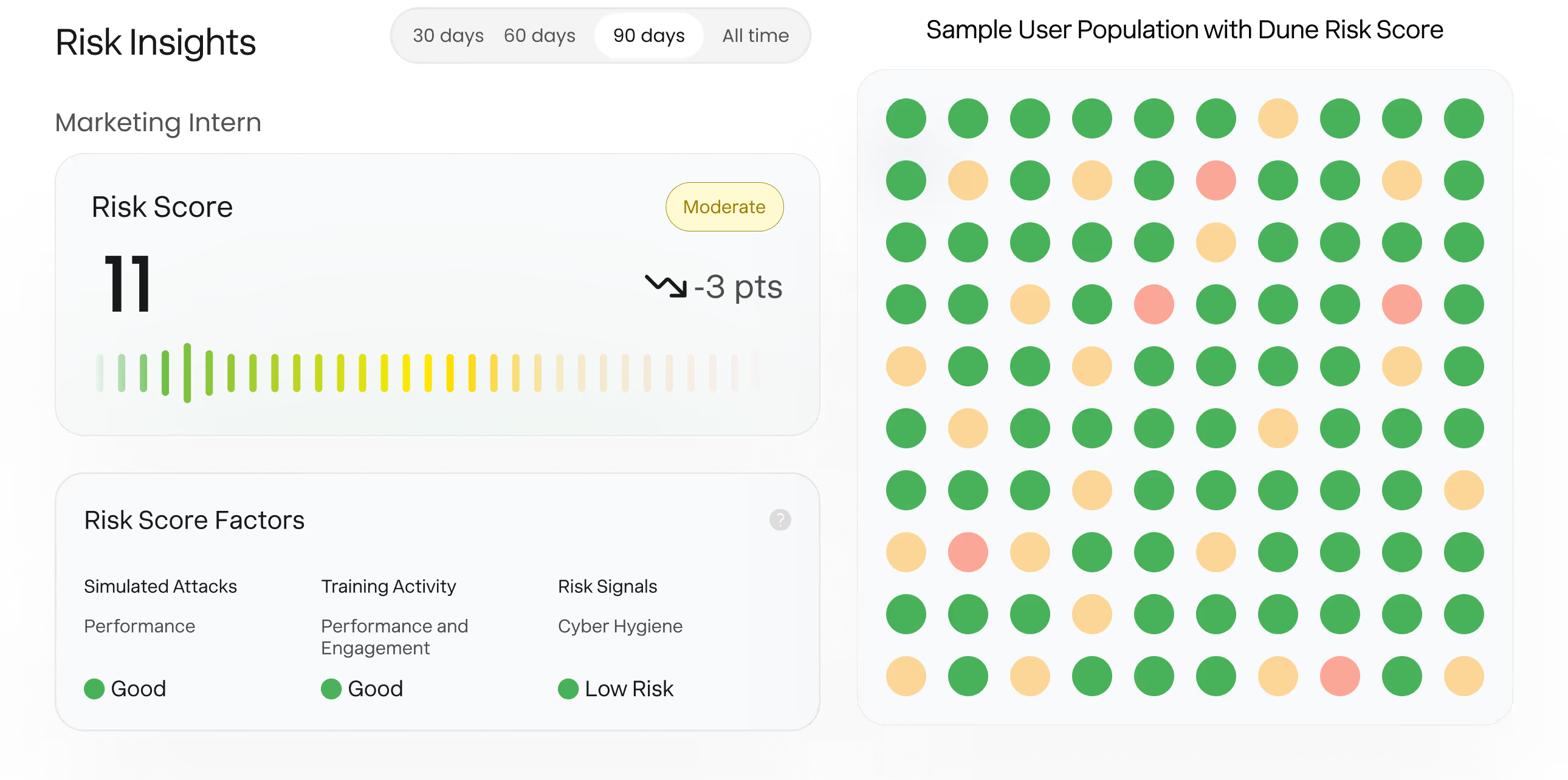
Dune Security continuously scores user risk using business impact, agentic attack simulations, training activity, and integrated risk signals, then automatically reduces that risk through microtraining, dynamic controls and targeted intervention.





Trusted by Fortune 1,000 Companies

.svg)






.svg)






.svg)





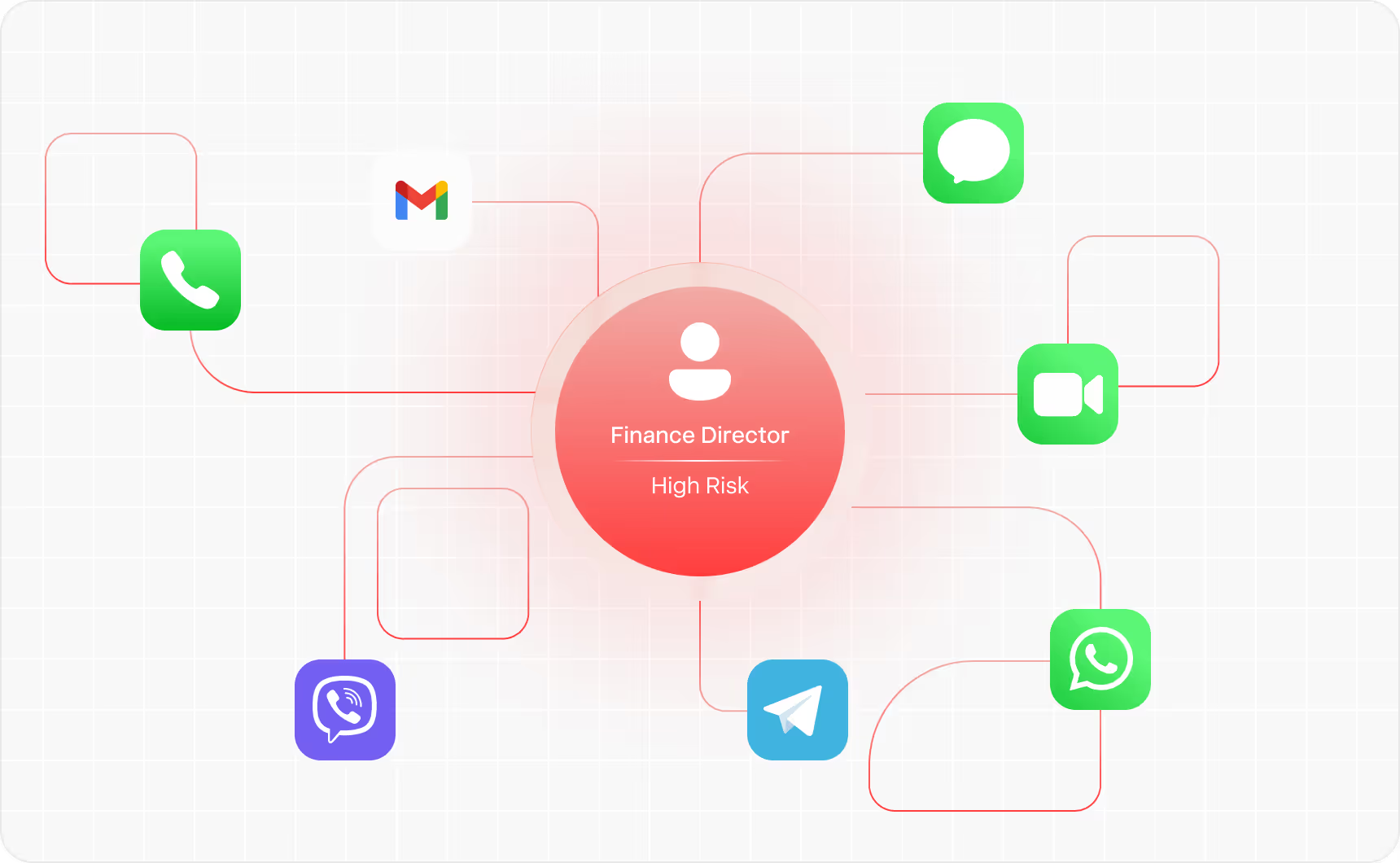
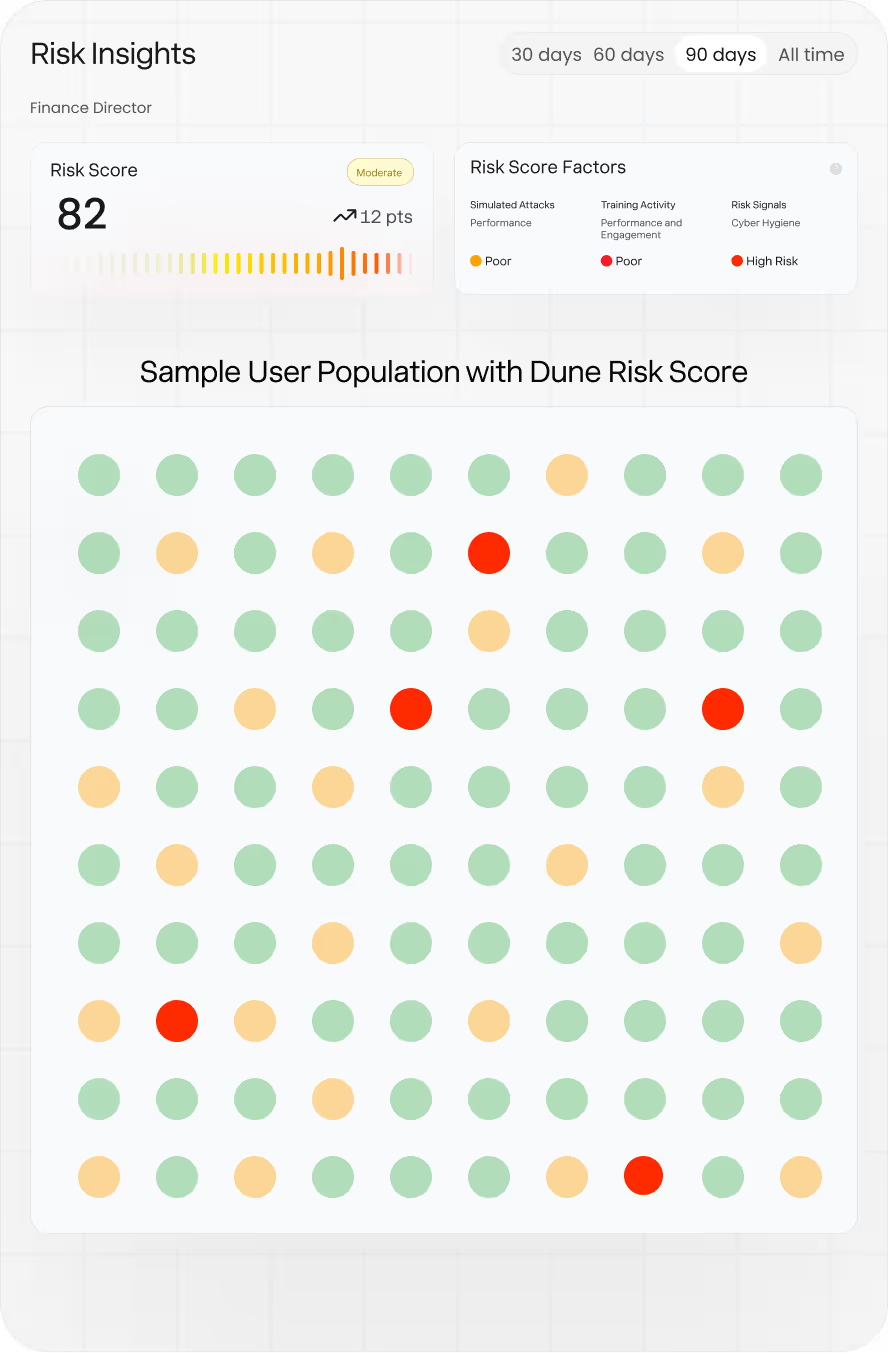
Expose User Risk
Using Real-World Signals
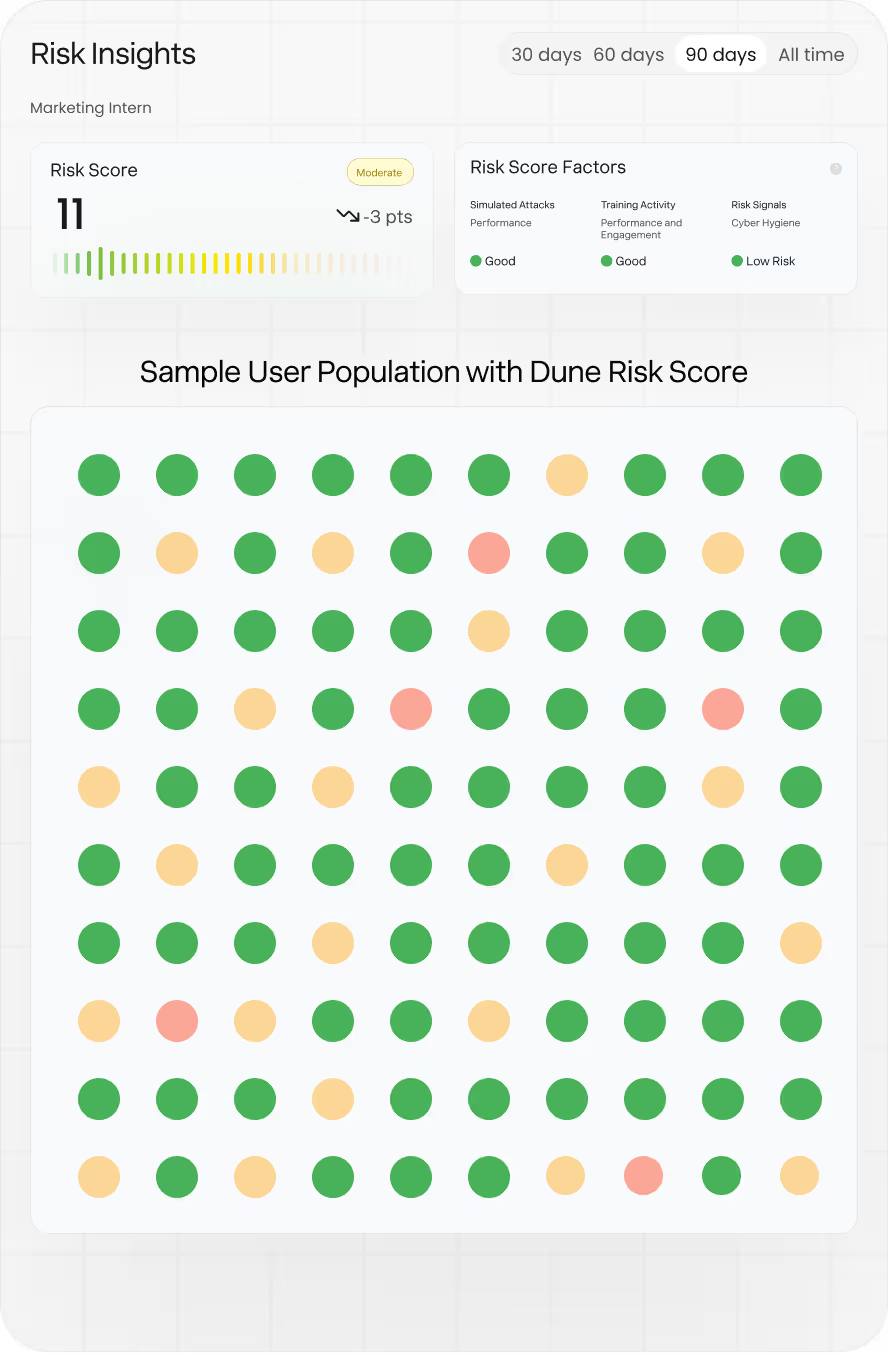
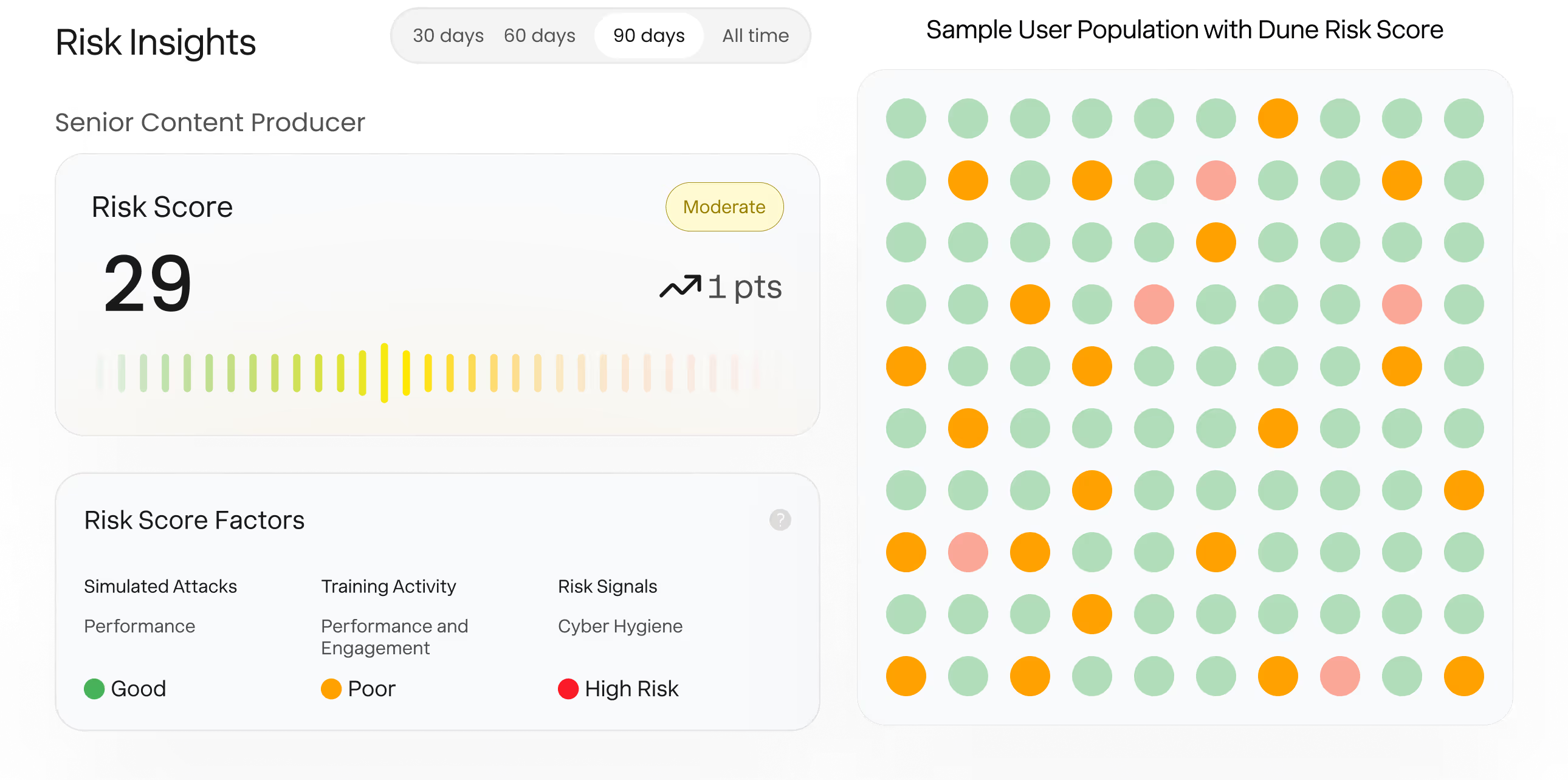
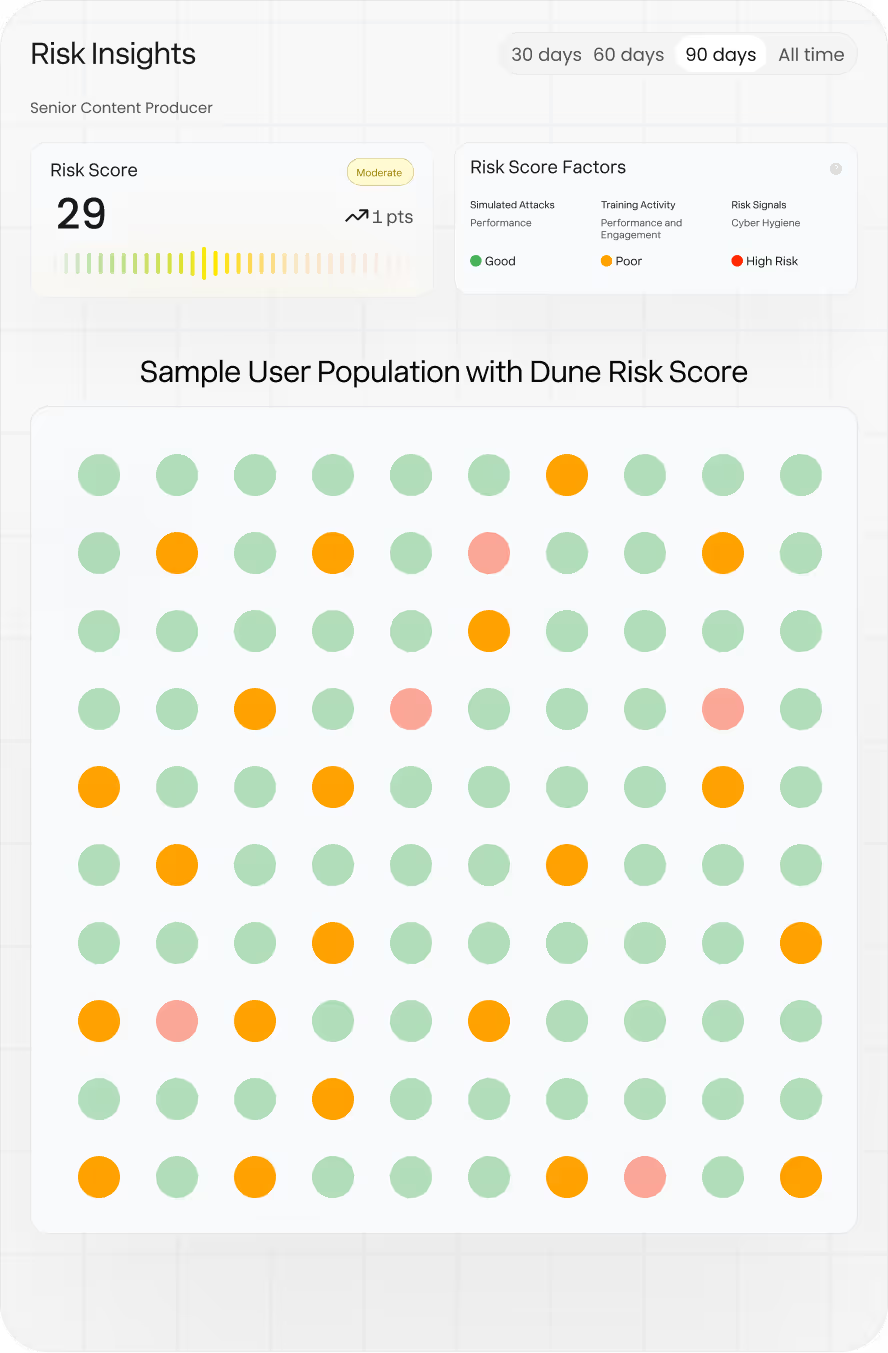
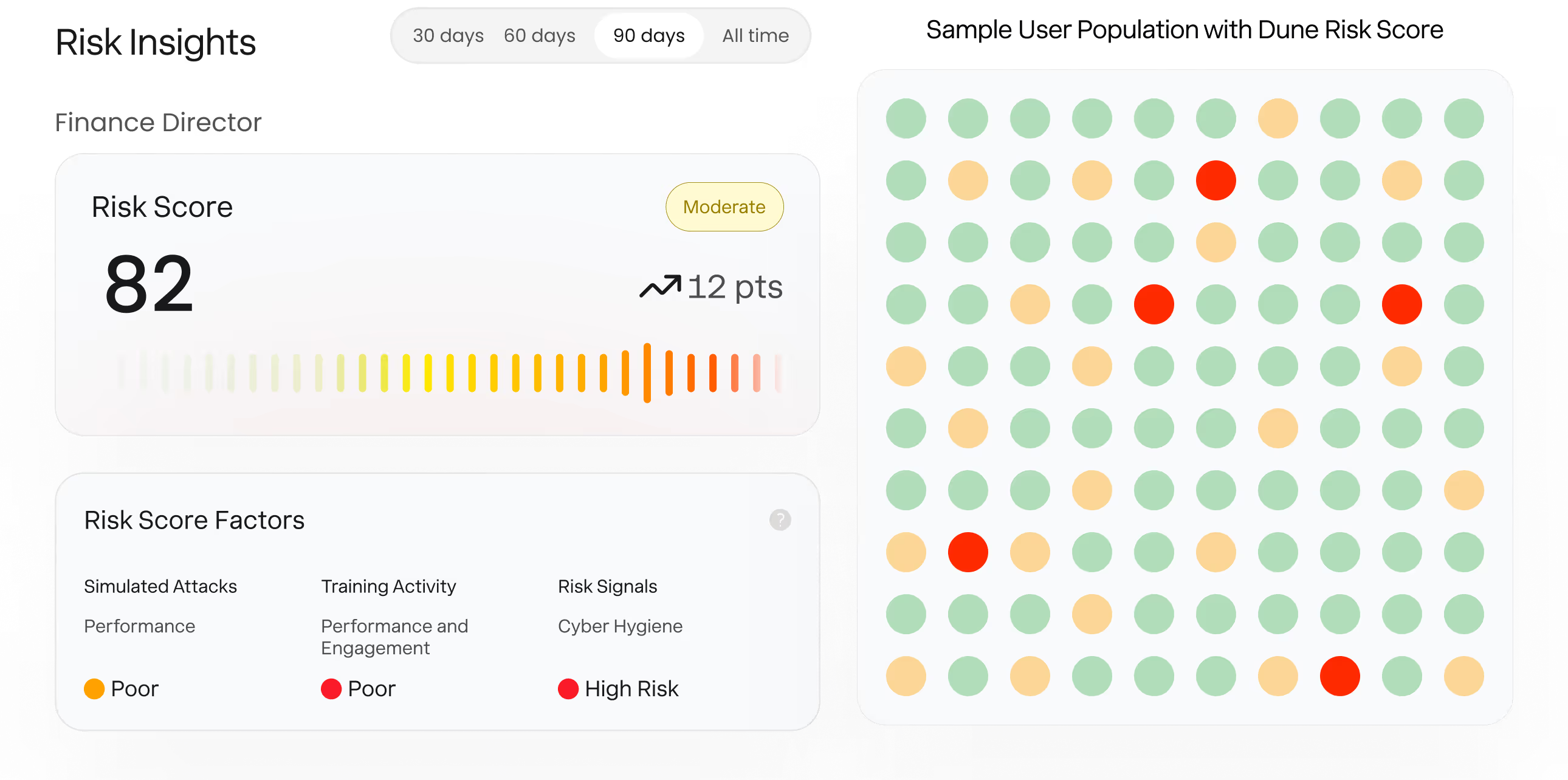
Correlates business impact, multi-channel social engineering behavior, integrated security signals, and training activity to surface the users who pose the greatest risk.
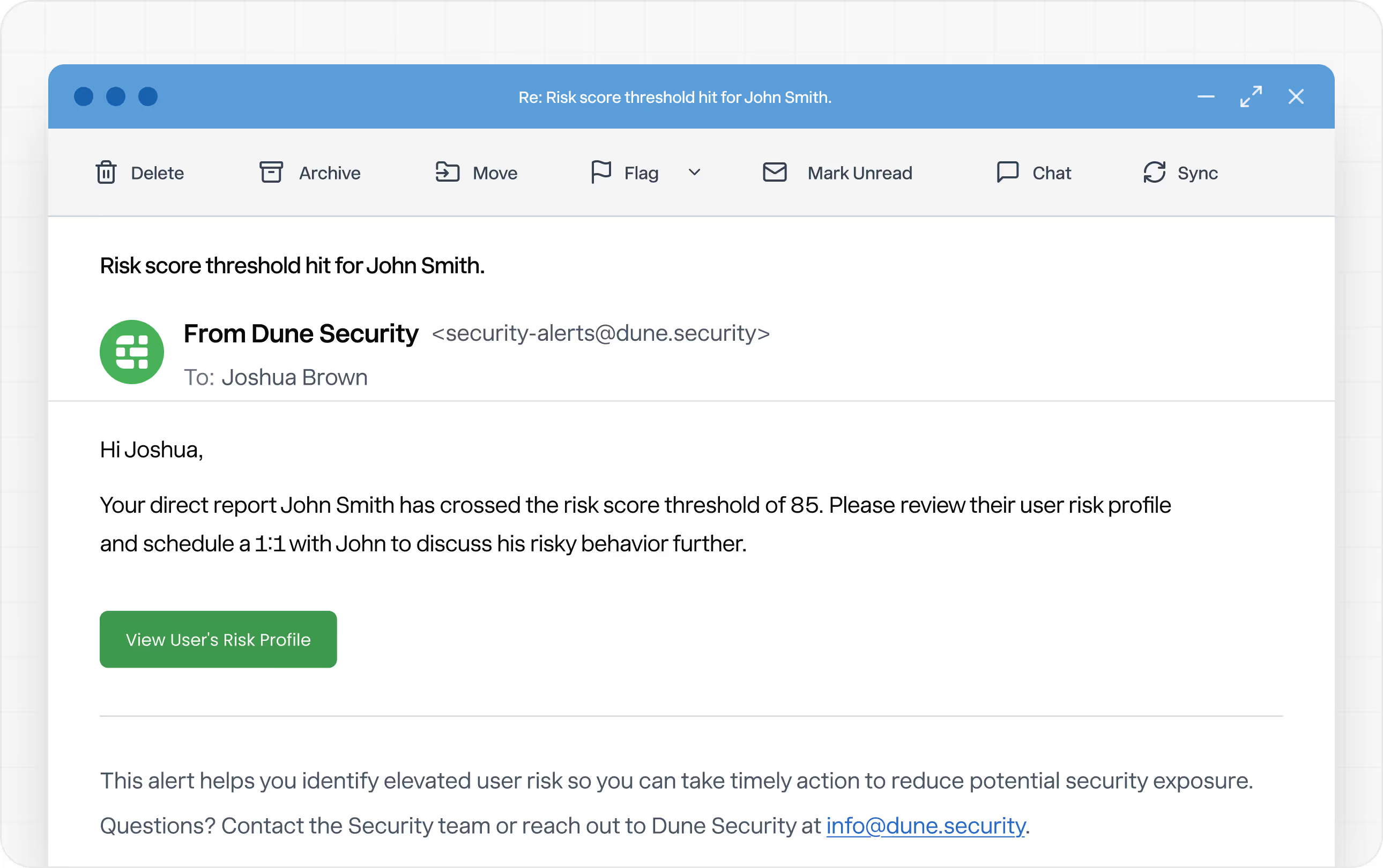
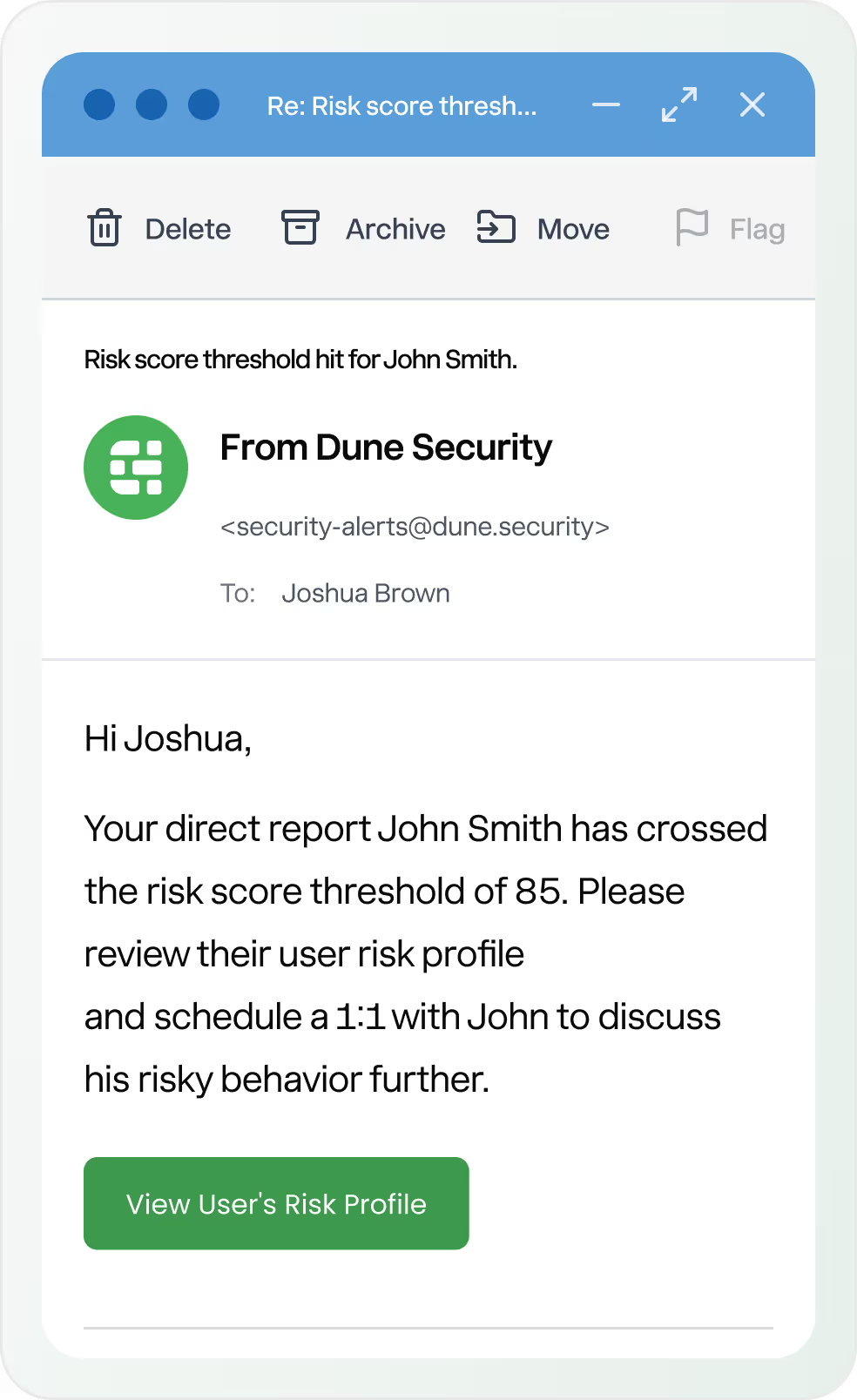
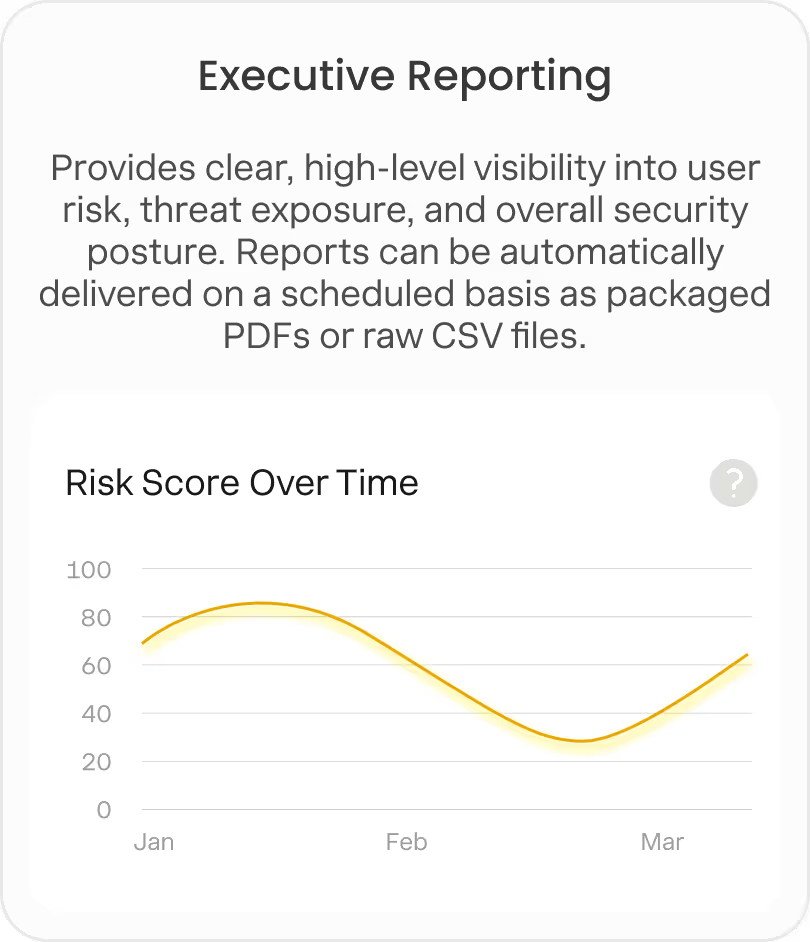
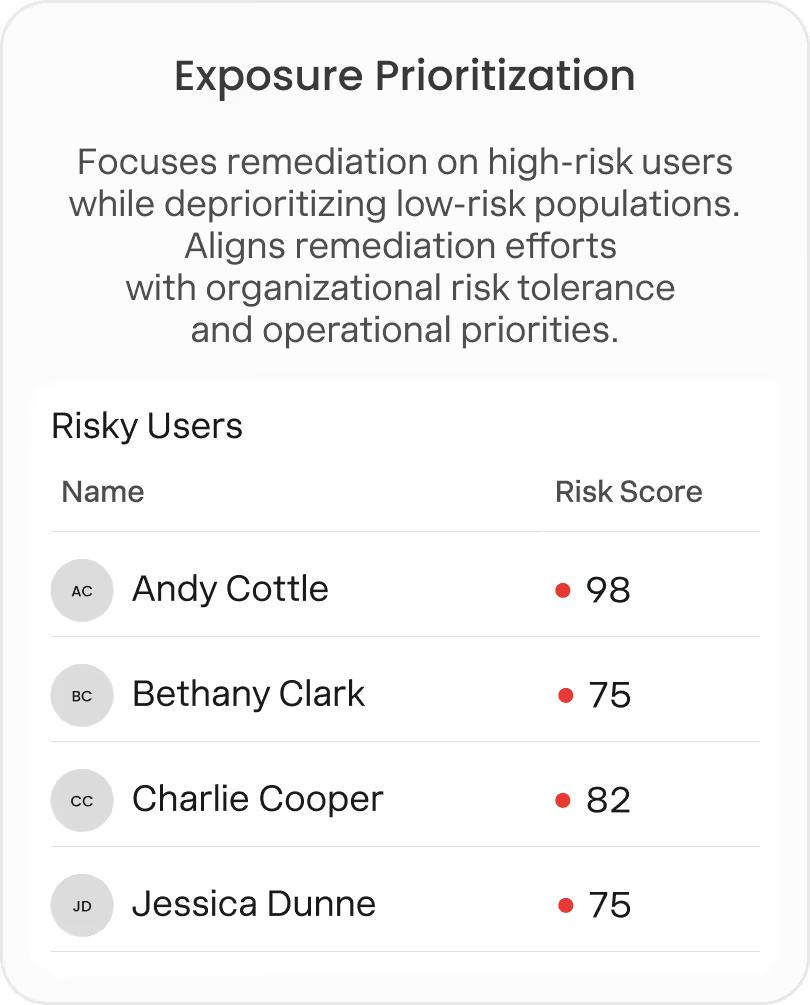
Identify High Risk Users
Converts raw inputs into executive-ready insight that highlights where risk is concentrated and where remediation will have the greatest impact.



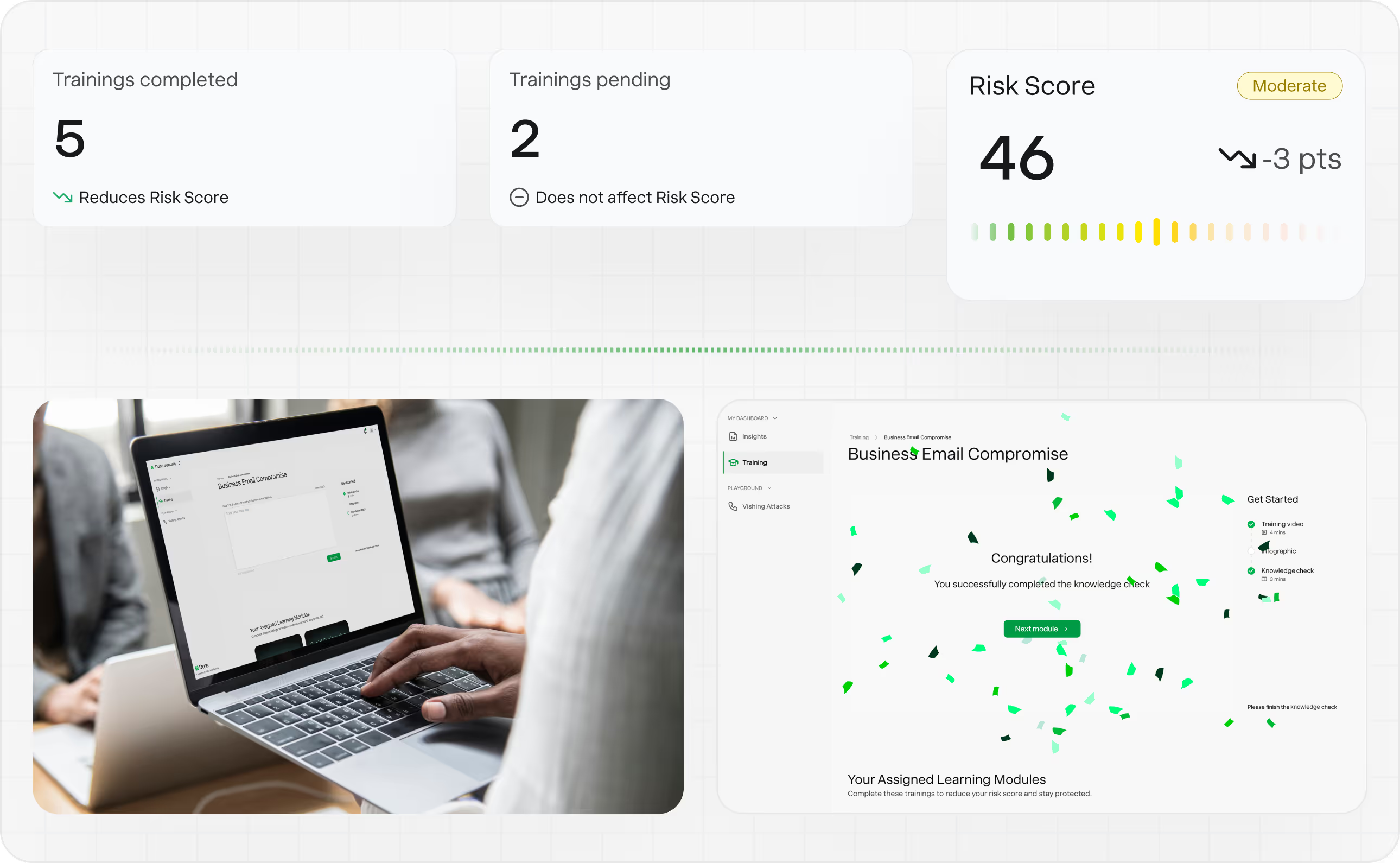
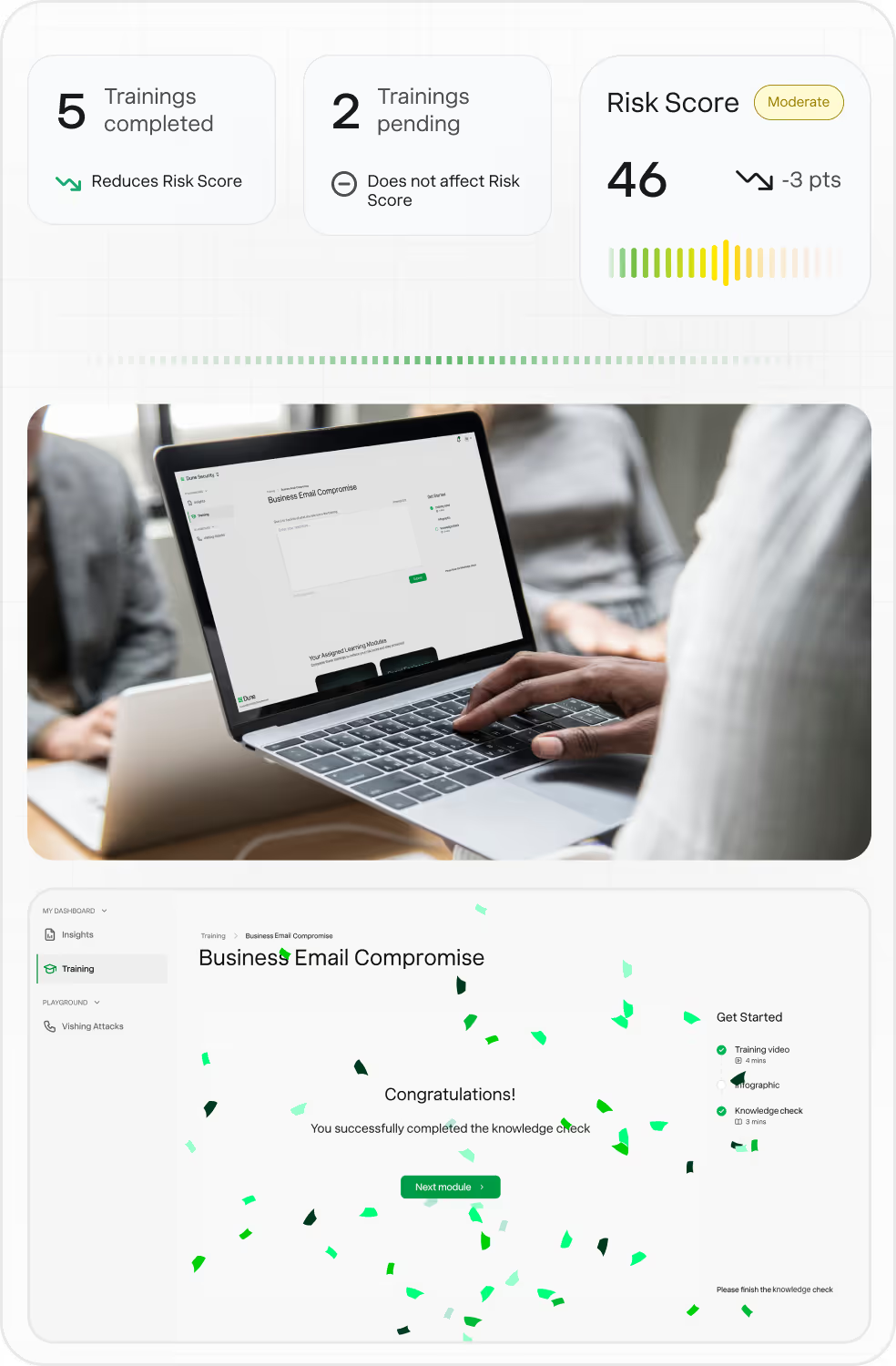
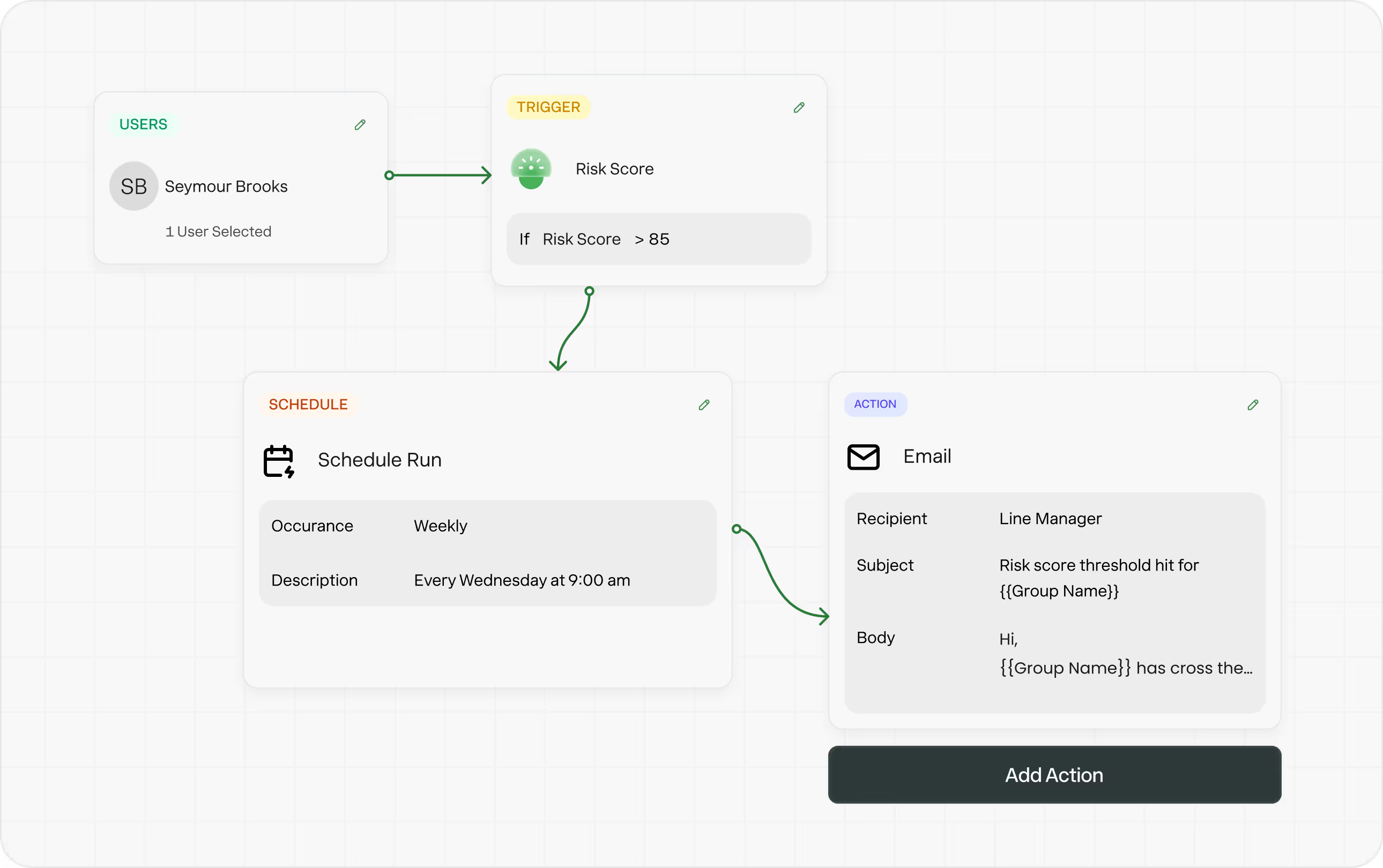
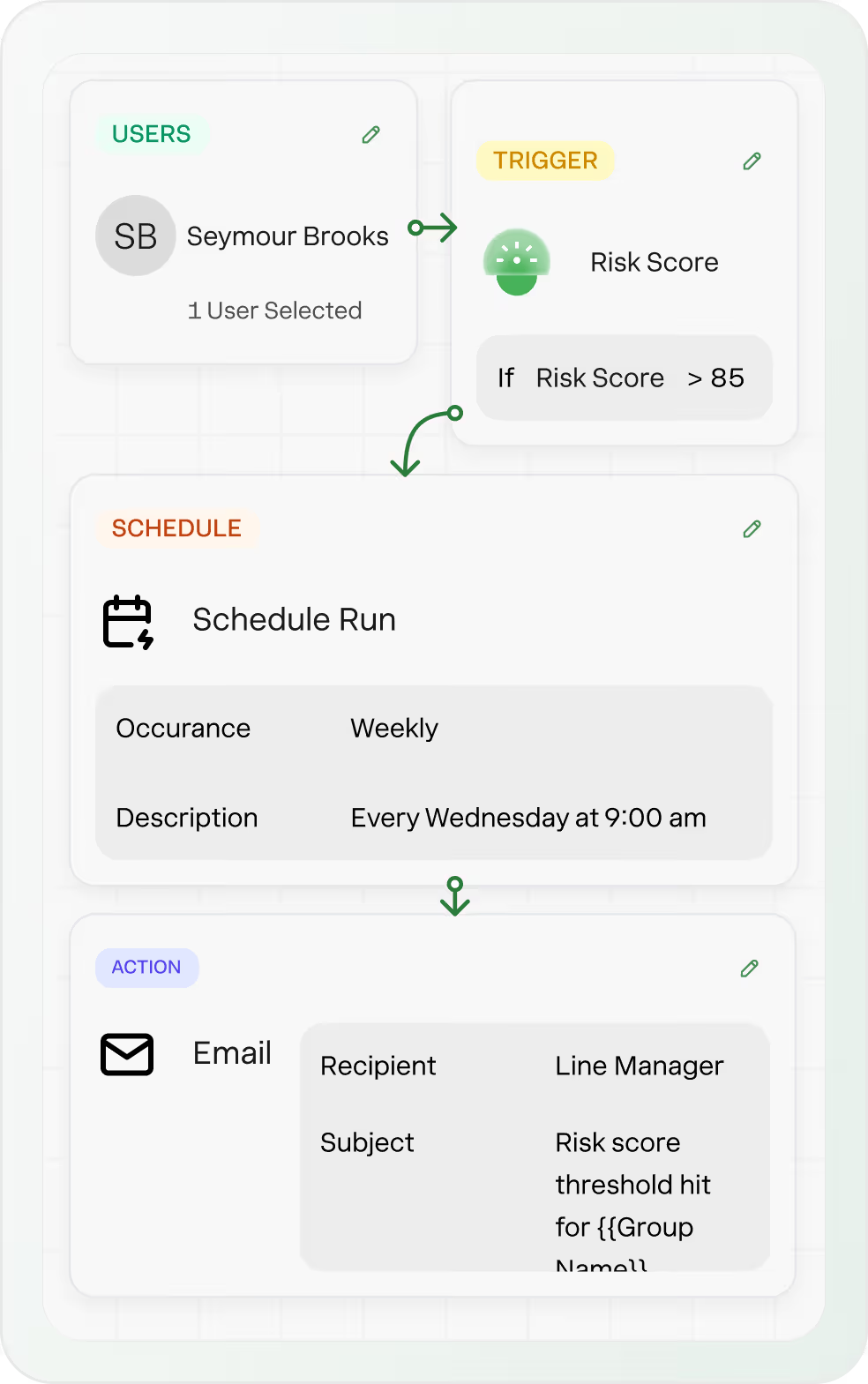
Automatically
Remediate User Risk
Delivers targeted training, enforcement, and controls that adapt to user behavior and reduce risk without slowing the business.
Get Started with Dune Today
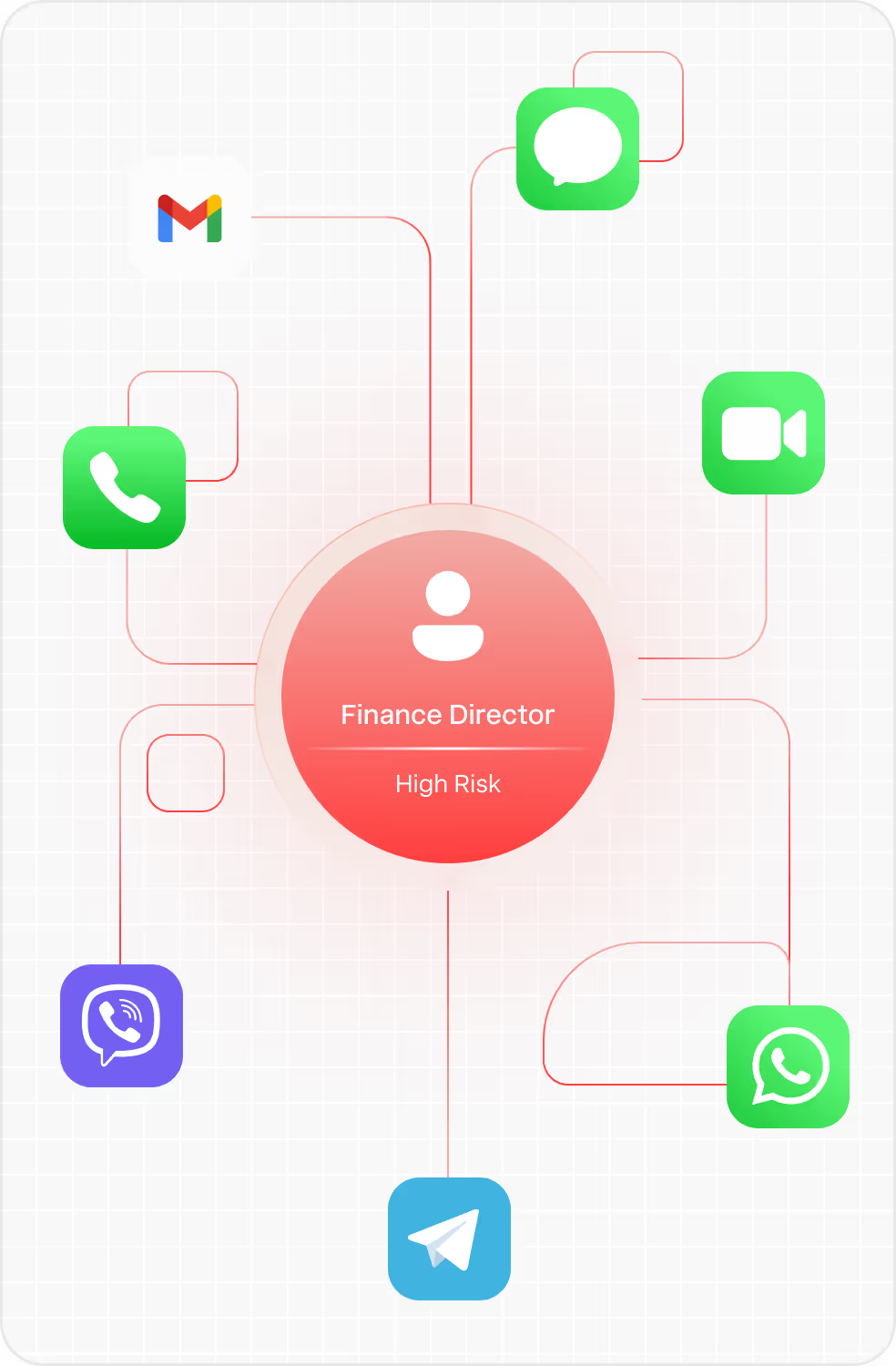
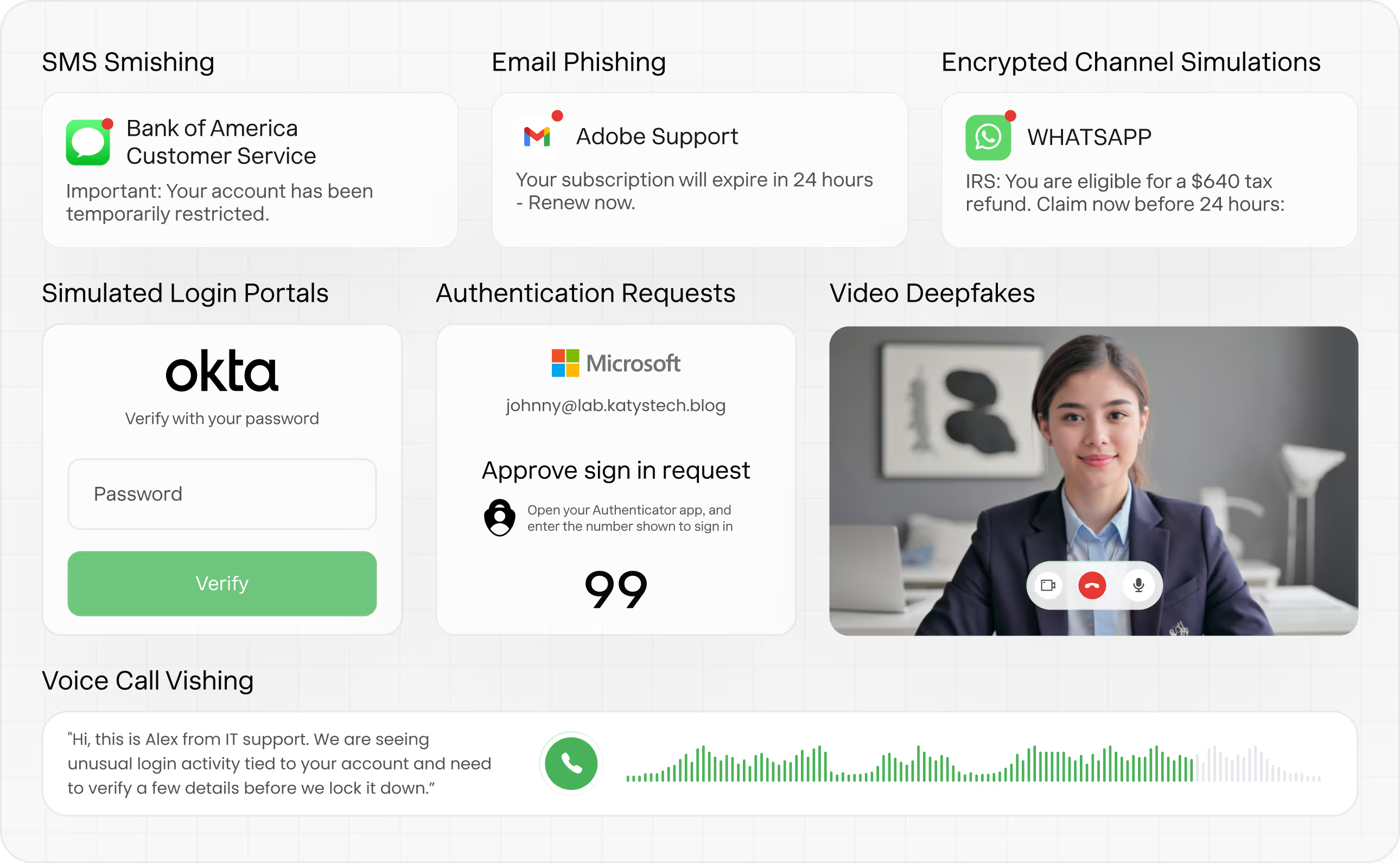
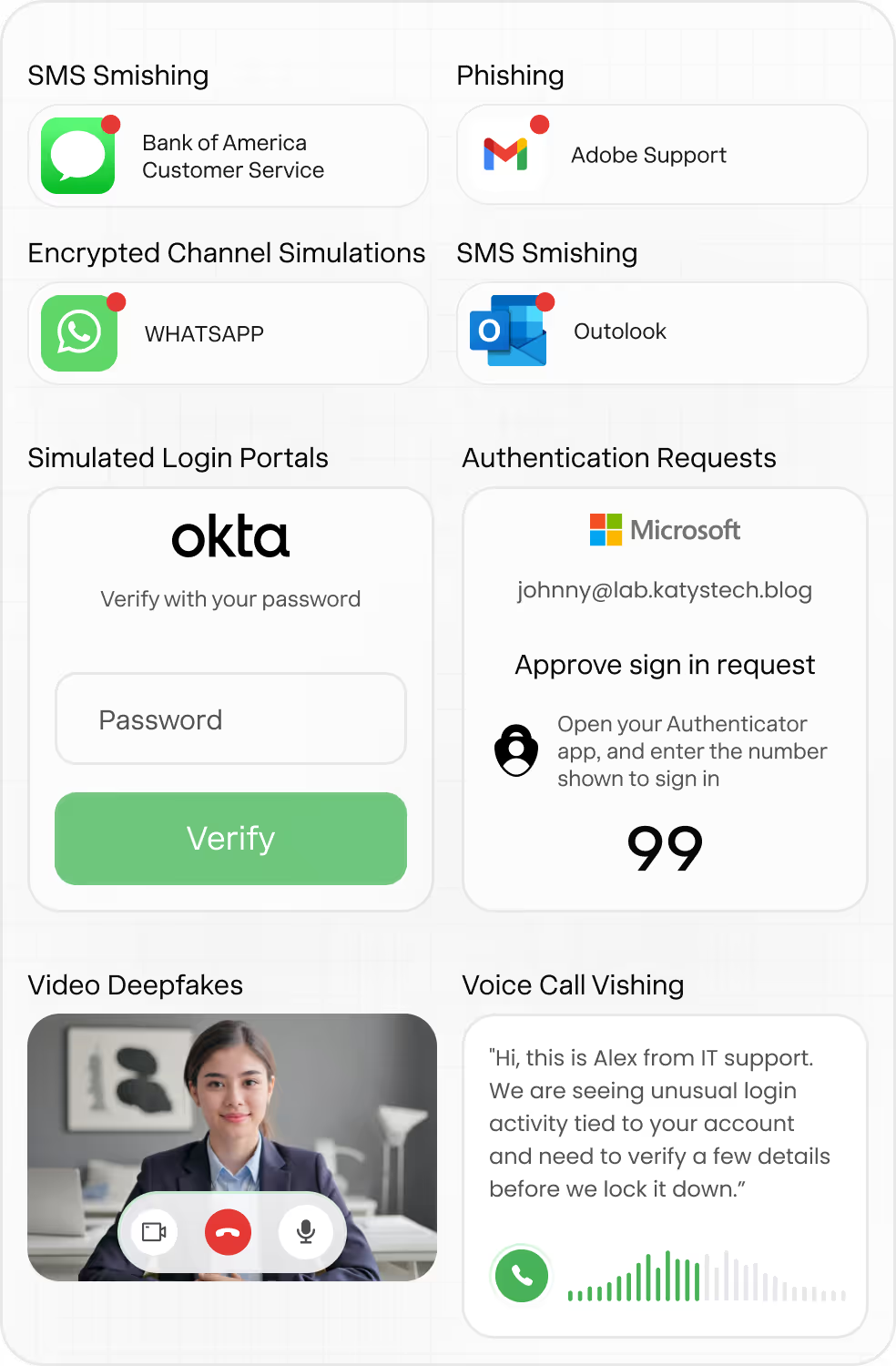
Agentic Attack Simulations
Models real-world social engineering and insider threat tactics across channels and conversations to reveal how users behave under realistic attack conditions.
GenAI Attacks
Targeted, point-in-time simulations powered by GenAI. Focus on specific decision points, such as clicking a link, entering credentials, or responding to a trusted request.

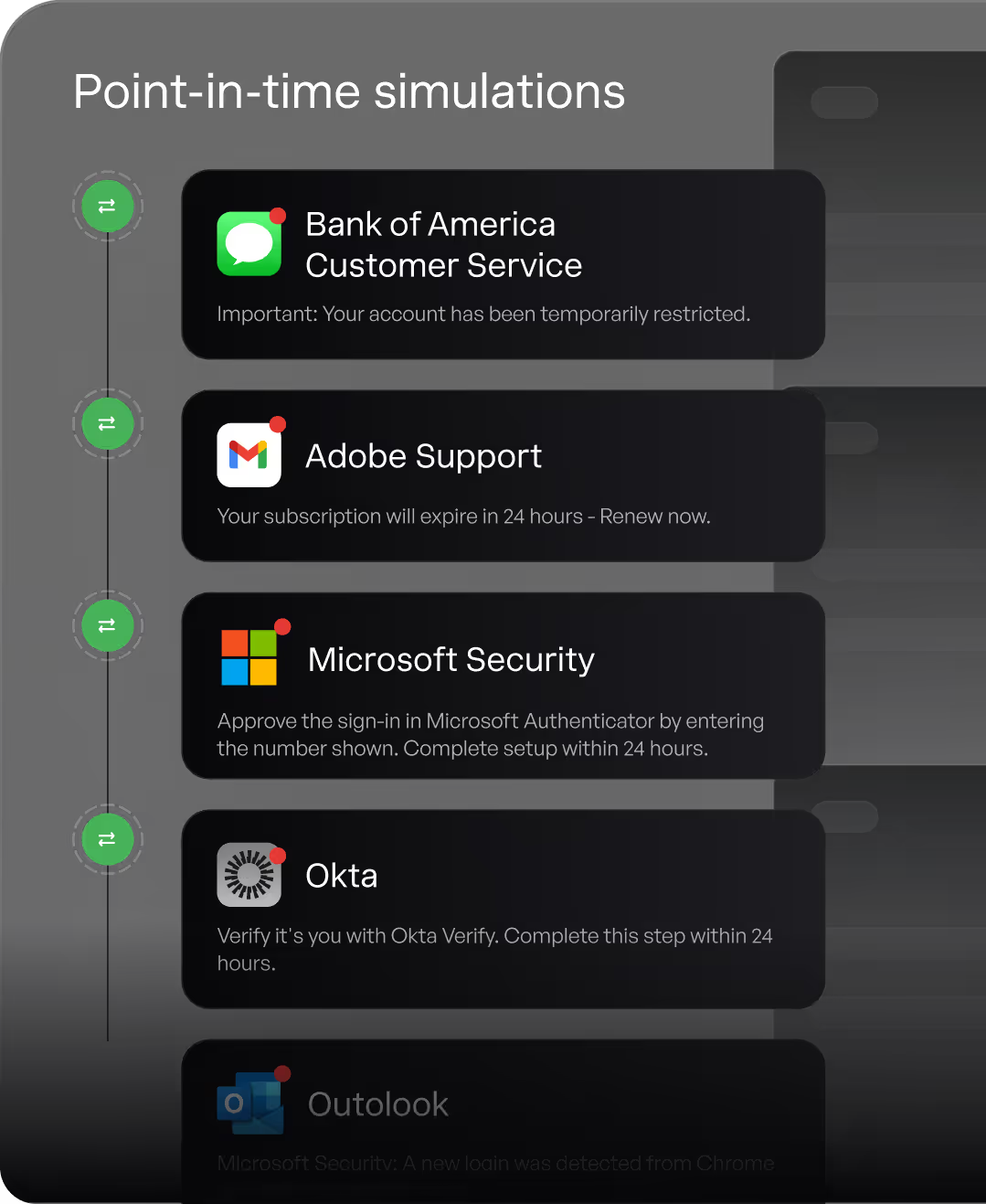
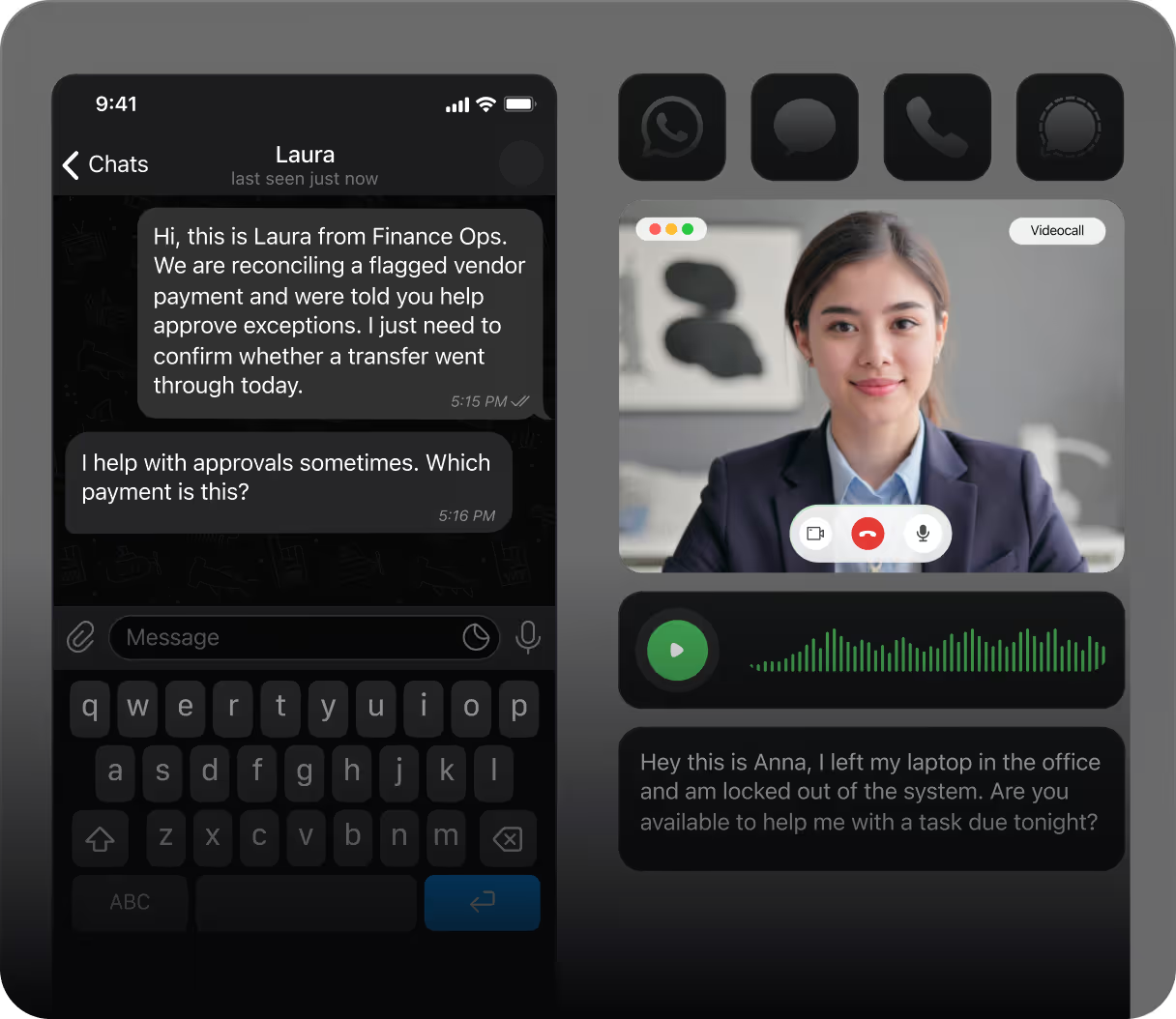
Conversational Red Teaming
Live social engineering simulations that unfold through ongoing conversations and adapt based on how users respond to escalated pressure, impersonated trusted identities, and shifted channels.
Explore Agentic Attack Simulations
Dune Studio
Training That Looks, Sounds,
& Feels Like Your Organization
Dune Studio is a fully managed, AI-powered cinematic training experience. It turns real-world risk into personalized learning tailored to your people and environment. The result is higher engagement, stronger retention, and measurable reductions in user risk.
Meet the Dune Studio Team
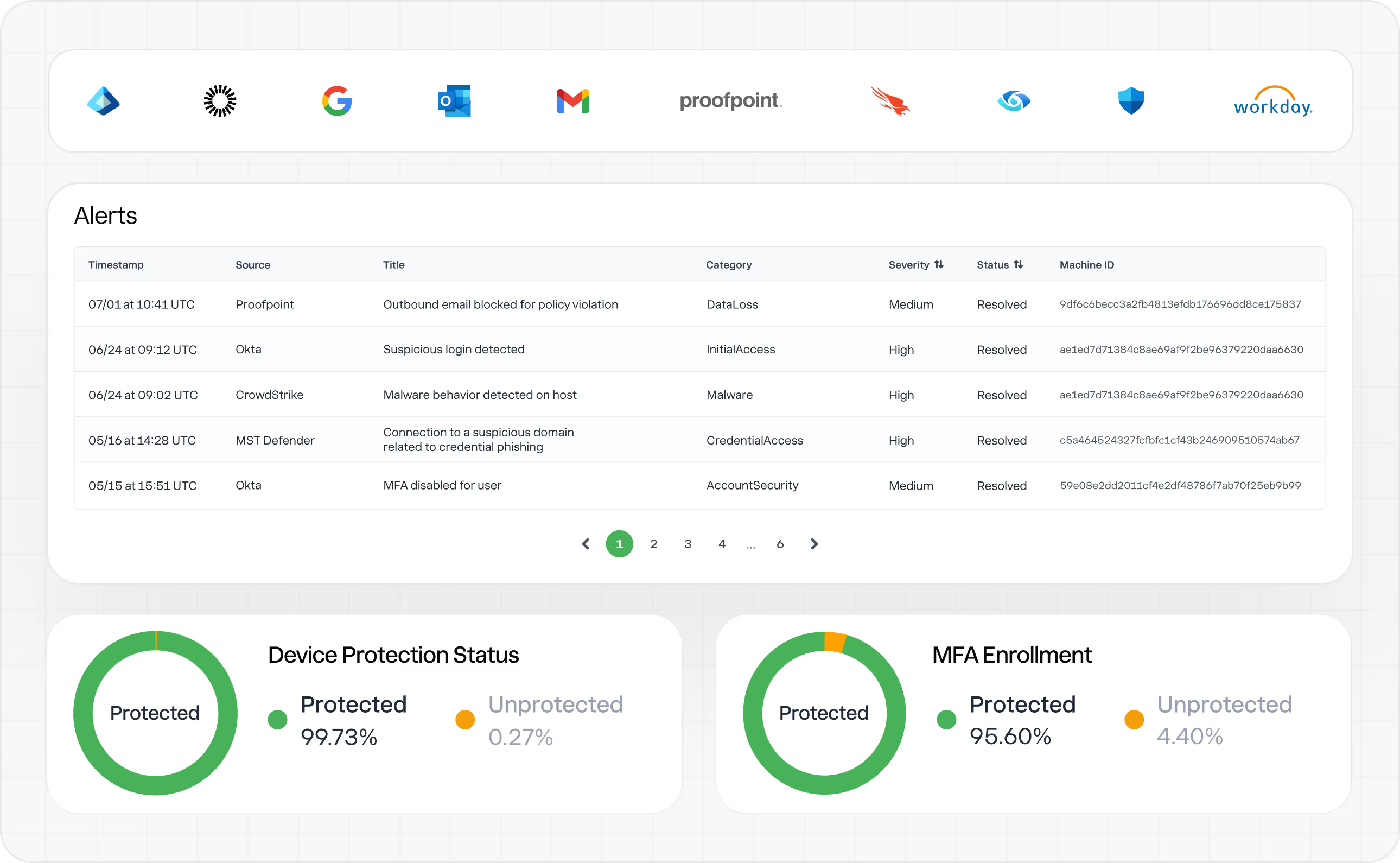
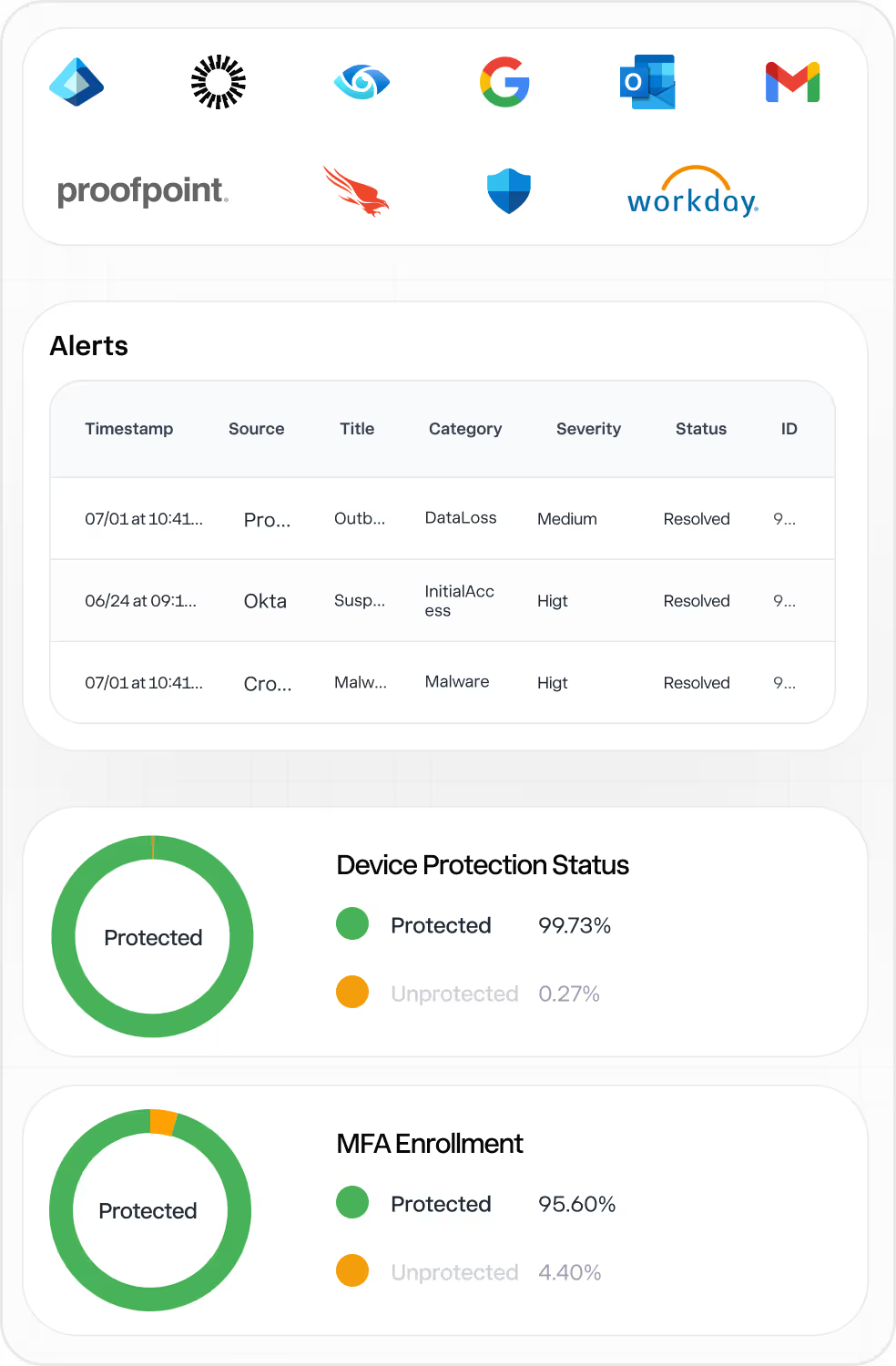
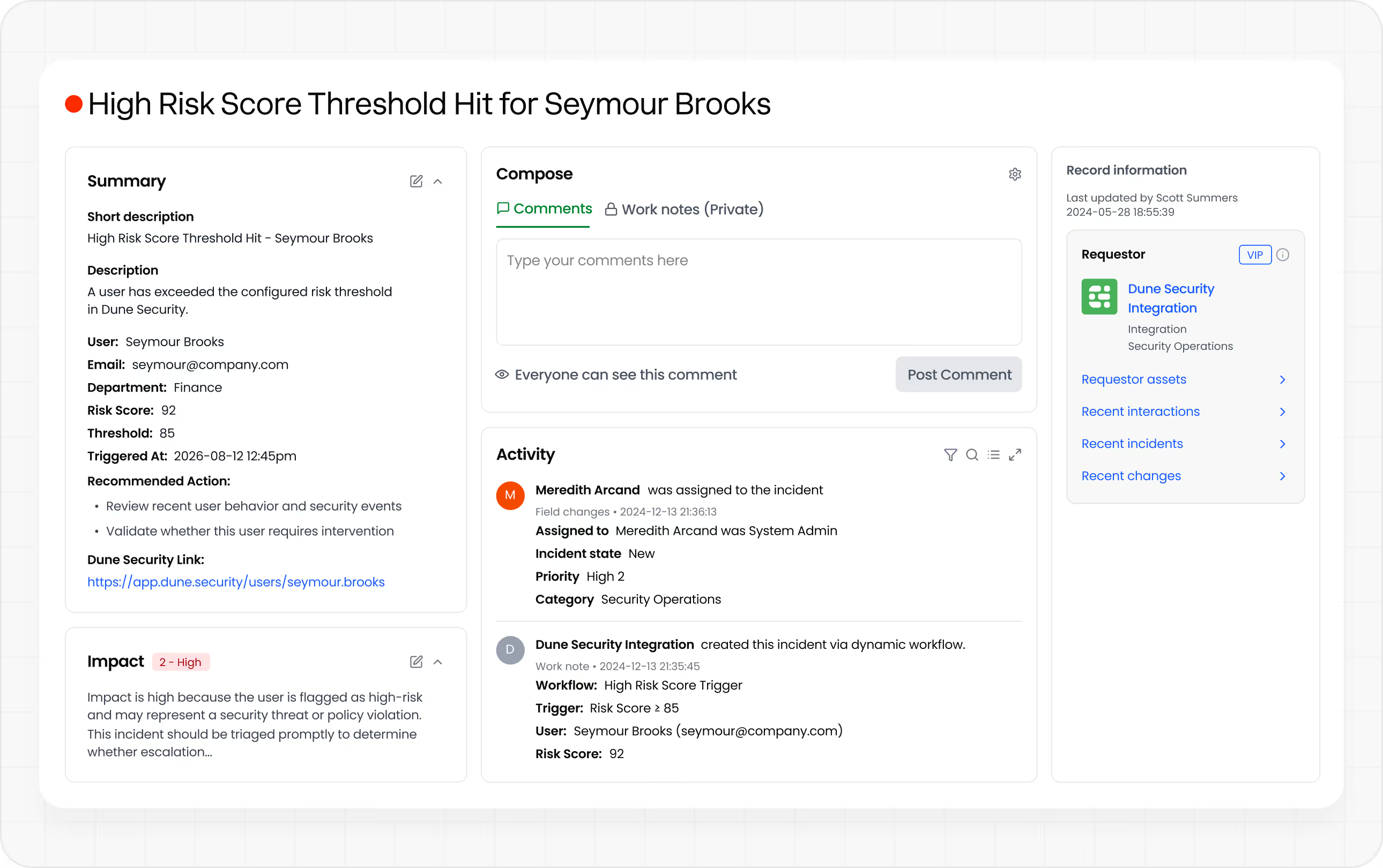
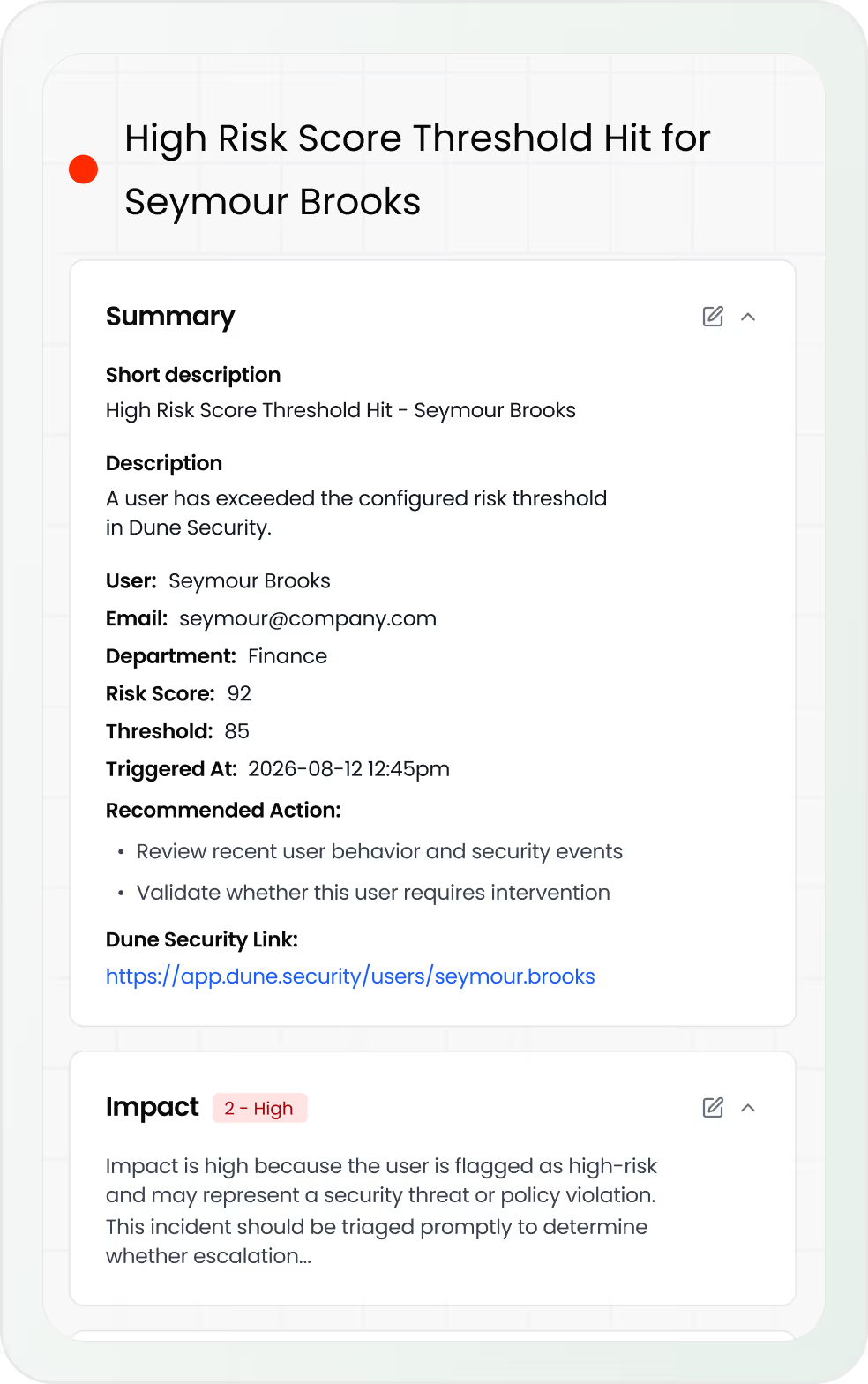
Risk Signal Integrations
Ingest unlimited signals from your security stack to build a single, continuously updated view of each user’s real-world exposure.
.avif)









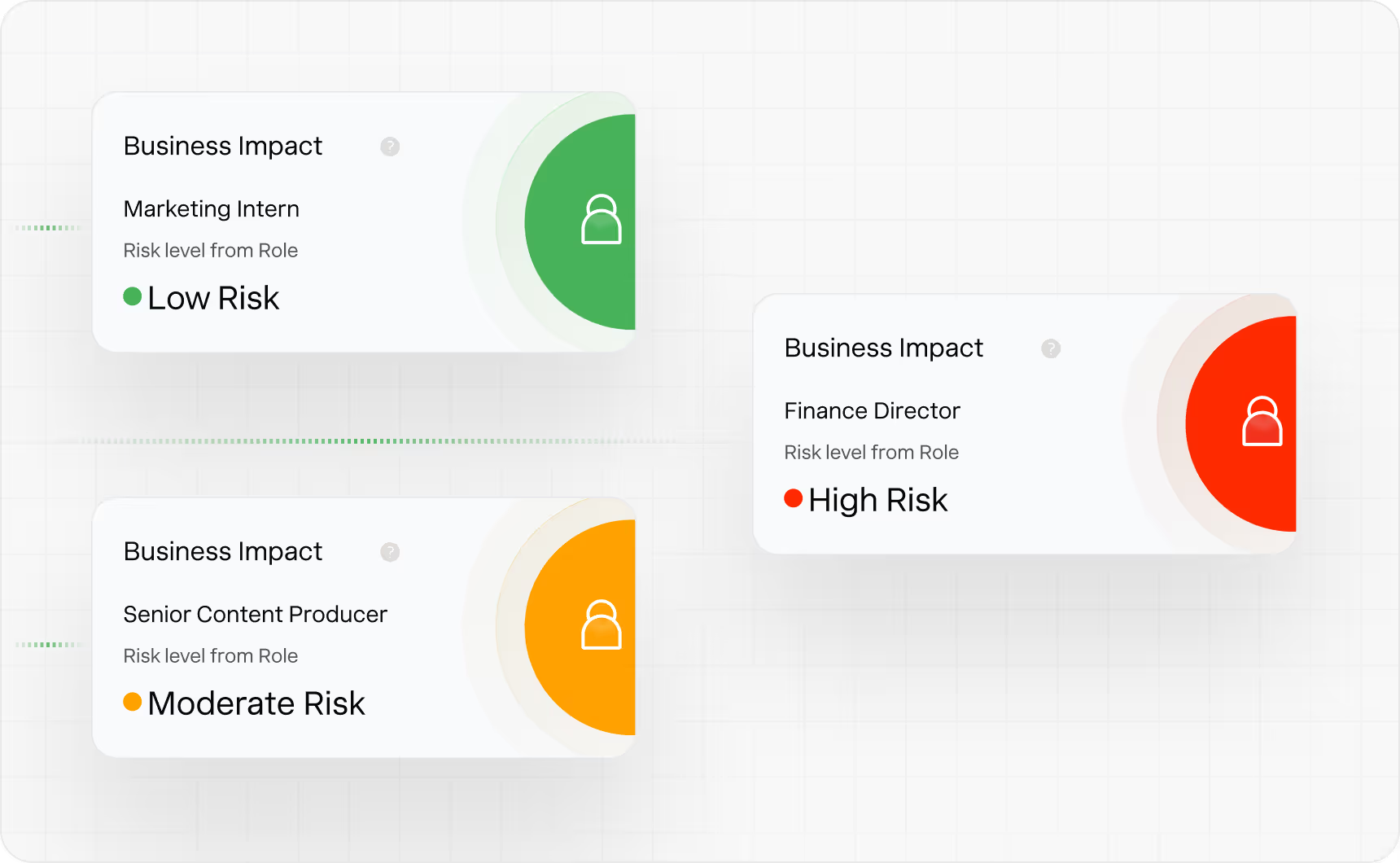
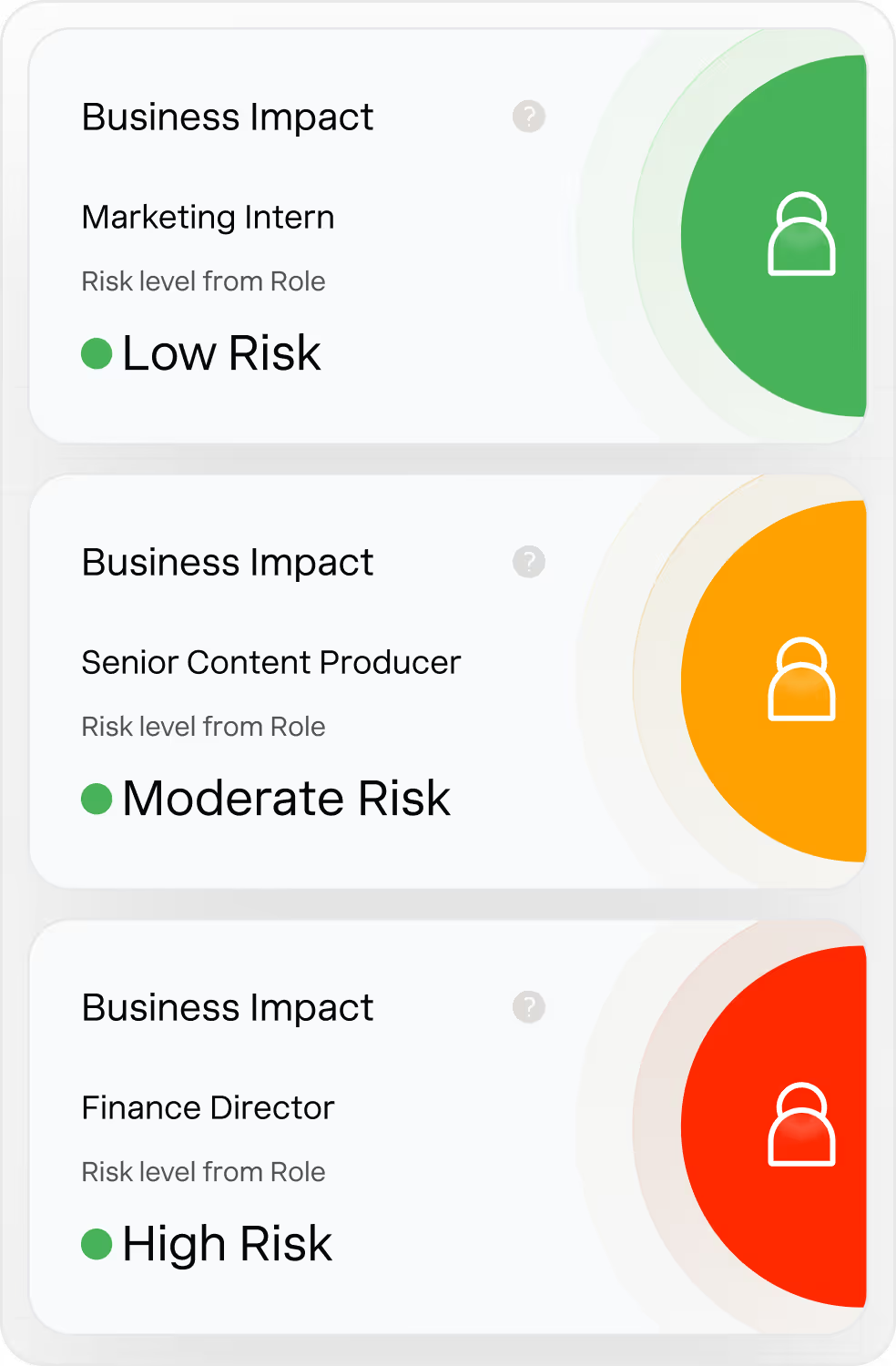
Custom Risk Score Weighting
Dune gives security teams direct control over how user risk is calculated. Tailor how each risk factor contributes to a user’s overall score so prioritization aligns with your real threat landscape, not a generic model. Adjust scoring for specific user groups where risk profiles differ.
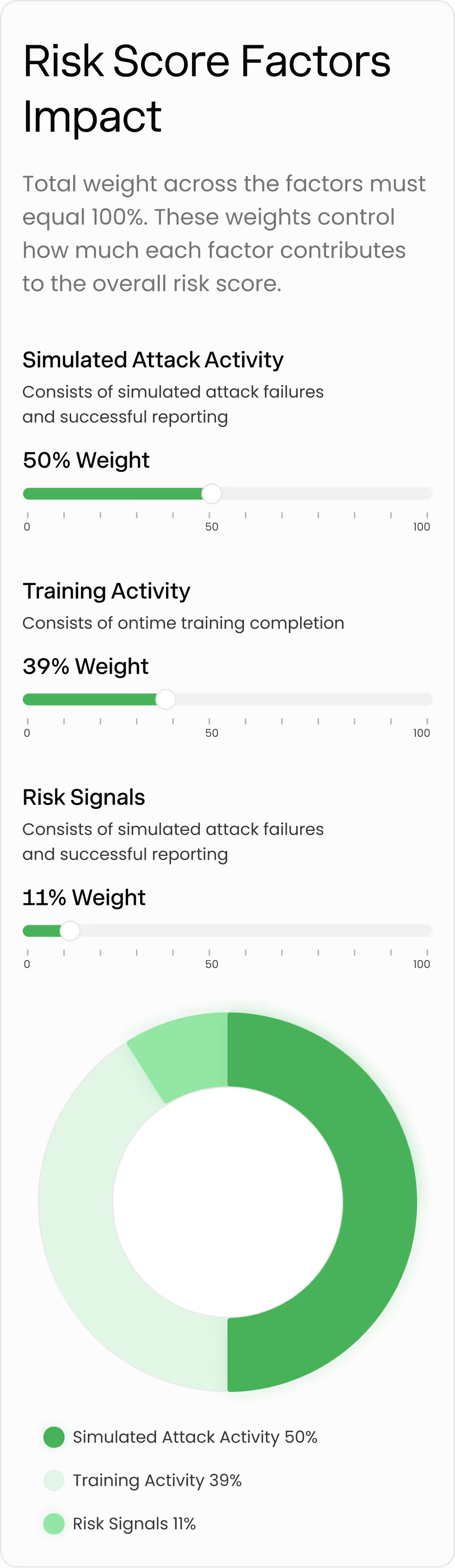
Each factor is assigned a percentage weight that determines its influence on the final score. All weights total 100 percent, making scoring transparent and predictable.
Business impact is applied automatically based on role and access, ensuring users with higher potential breach impact are appropriately prioritized through built-in risk floors.
Scalable and secure for the world’s largest companies
Frameworks

Certified – Jan 2024 & Jan 2025

Certified – Aug 2024

Compliance Verified – Jan 2025

Compliance Verified – Jan 2025

Third-Party Attested – Apr 2025

Third-Party Attested – May 2025
Ready to protect your company & employees from social engineering attacks?