Insights on User Risk and Enterprise Security
Expert analysis, emerging trends, and the latest product, feature, and company innovations from the team redefining how enterprises think about user risk.




The Top User-Driven Cyber Threats Targeting Law Firms
Law firms sit on some of the most sensitive and valuable data in the enterprise, and attackers have built an entire playbook around exploiting the users who handle it. Learn how four dominant threat vectors are targeting legal sector workflows in 2026 and what it takes to stop attacks at the User Layer.




The Workforce Has Expanded: How Attackers Are Targeting Enterprise AI Agents
AI agents are being deployed across the enterprise at scale, and attackers have already started engineering against them. Learn how agentic AI expands the enterprise attack surface in ways legacy security programs were never designed to defend.
.avif)
.avif)


Making Cyber Risk Board Ready: Strategies for Winning Boardroom Confidence
Winning board confidence on cyber risk requires more than technical reporting. Security leaders need to support better governance decisions and communicate exposure in a way directors can act on.
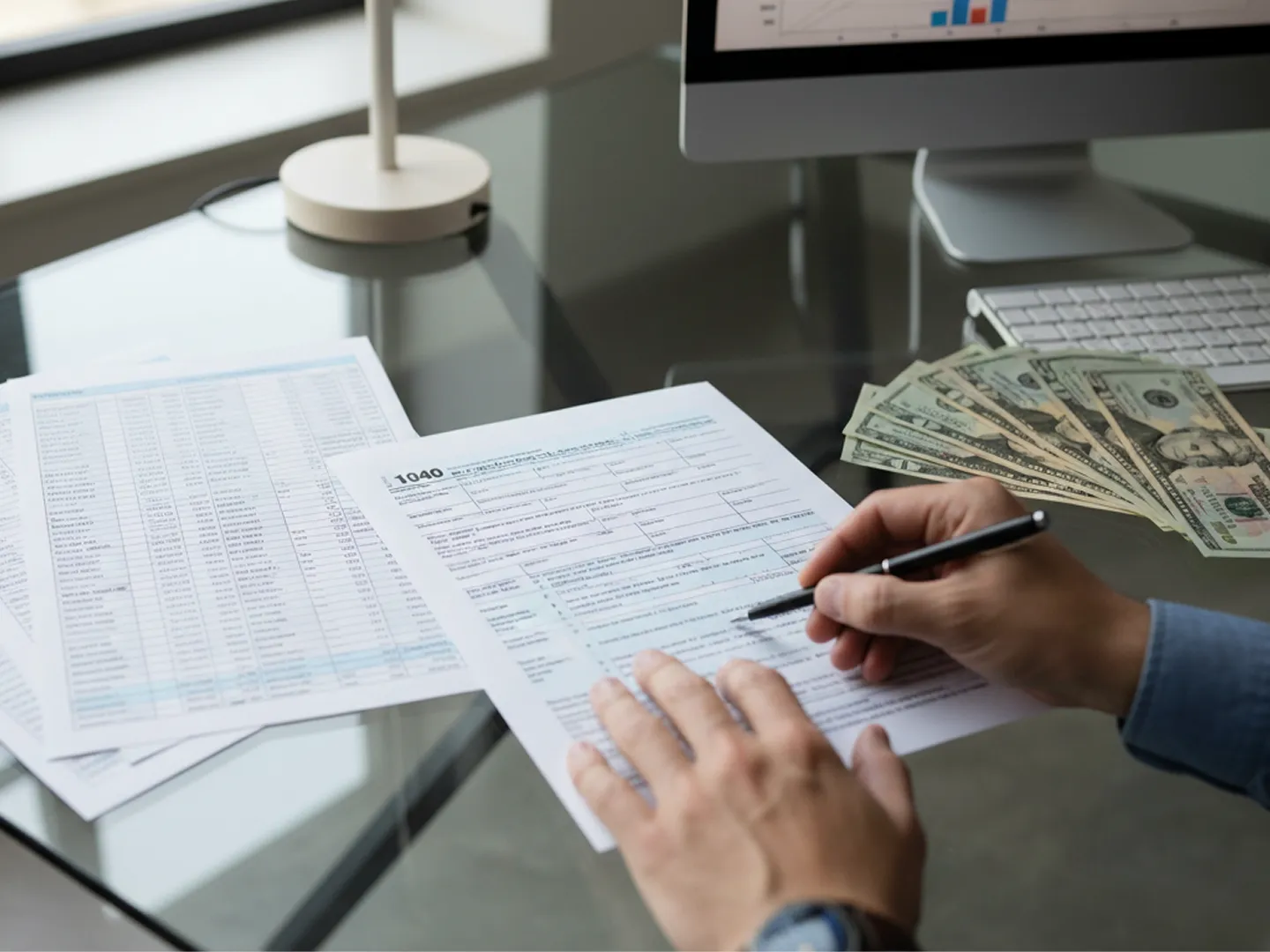


Tax Season Scams: How Refund Fraud Escalates Into Enterprise Risk
Each filing season, threat actors execute coordinated, identity-driven campaigns that begin with refund fraud and rapidly escalate into credential harvesting and enterprise exposure.
%20(1).avif)
%20(1).avif)


Dune Security and OmegaBlack Partner to Deliver Intelligence-Driven Protection for the User Layer
Threat actors are building their campaigns across the dark web long before they reach the enterprise. Dune Security and OmegaBlack are partnering to deliver layered protection that connects external exposure with user level risk scoring and automated remediation.




How Attackers Exploit Trusted Access in BPO Environments
Learn why BPO environments are increasingly targeted by social engineering and how user cyber risk spreads across outsourced operations and client organizations.




How Impersonation-Based Social Engineering Drives Enterprise Cyber Risk
Impersonation-based social engineering attacks are driving disproportionate enterprise risk. Learn why they work and what it takes to defend against them.




Cybersecurity in Healthcare: How Social Engineers Target Patient Data and Hospital Operations
Healthcare’s reliance on digital systems and high-pressure clinical environments has made user risk a patient safety issue, and organizations must rethink how they prepare their workforce for modern attacks.


Dune Security and Abstract Security Partner to Deliver Real-Time Detection and Automated Risk Reduction
Modern attacks often reveal themselves through subtle technical events that most tools miss until it is too late. Dune Security and Abstract Security now bring real-time detection and automated risk remediation into a single defense strategy.


