Dune Security Takes Over Times Square
In less than three years, Dune Security has grown from an idea into a platform trusted by Fortune 1,000 enterprises. Our Times Square milestone celebrates that journey and our mission to stop insider threats and social engineering at scale.
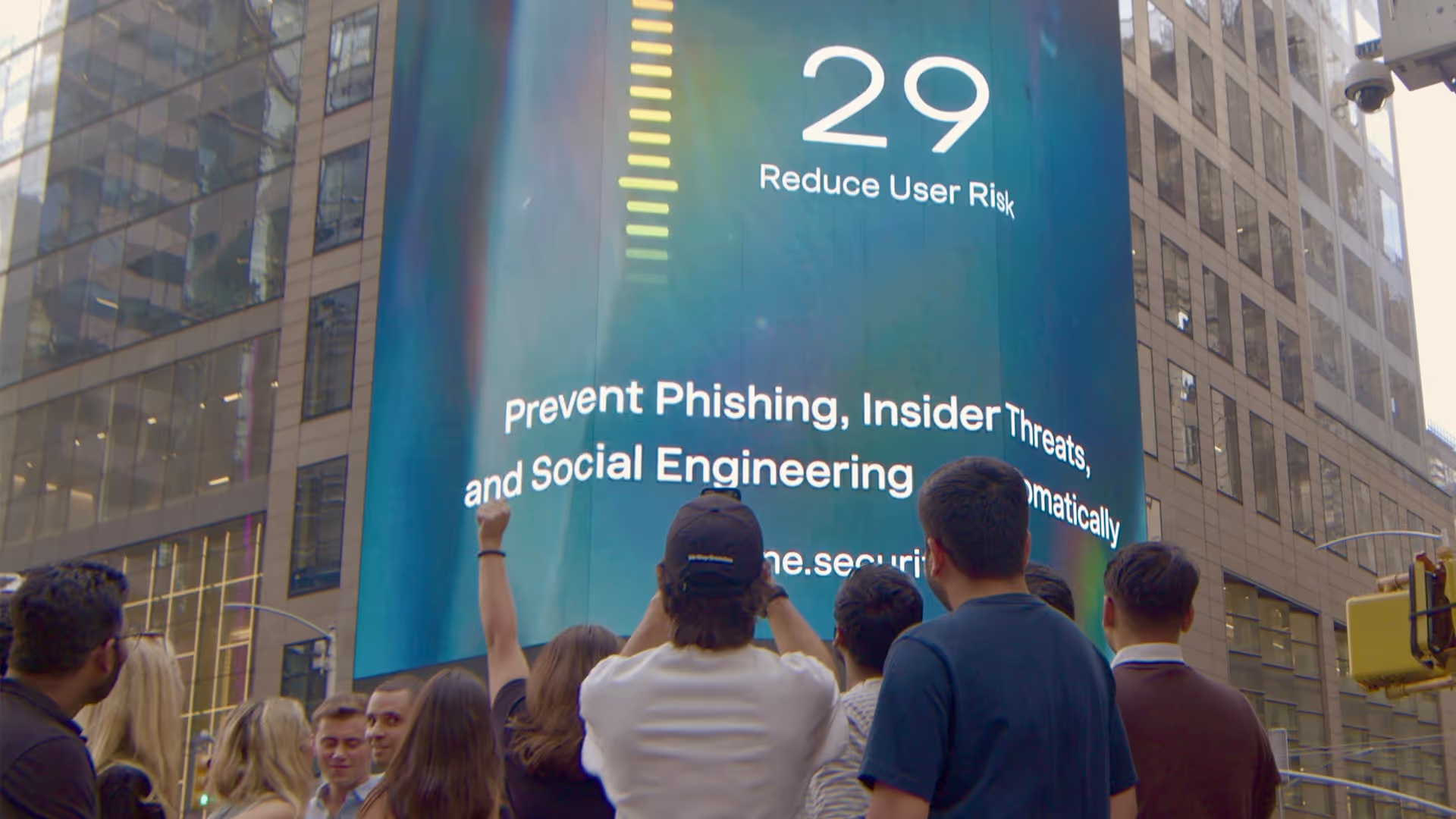
Yesterday, our team stood in Times Square to witness Dune Security unveil its mission to prevent insider threats and social engineering across a six-story billboard display. A rare marketing milestone for a seed-stage company, this unique brand moment reflects both the urgency of the threat landscape and the momentum behind our growth.
As Michael Waite, our CTO and Co-Founder, put it: “In under two and a half years to see this business go from just a nebulous idea to something that's being showcased in such a public space, meeting such a high-demand area within cybersecurity is amazing.”
Dune Security was born out of a serendipitous meeting between Co-Founders David DellaPelle and Waite, who met as strangers during a cybersecurity incident that grounded flights at JFK. Since then, Dune has raised $8 million in funding, experienced rapid growth, and earned the trust of Fortune 1,000 enterprises facing some of the most persistent security challenges in the world.
The team has evolved into a company recognized for addressing one of the most urgent and complex problems in cybersecurity: user risk. From our Tribeca office, we design, test, and deliver a platform that comprehensively quantifies and individually reduces user risk – stopping the attacks that bypass legacy defenses and exploit human behavior. The result is stronger protection today and lasting resilience for what’s ahead.

Bringing the entire team to Times Square to see our mission projected above the city was a well-deserved celebration for the relentless work happening behind the scenes. It also served as a reminder of why we exist: to enable enterprises to move forward without fear of being blindsided by threat actors.
Equally critical are the partnerships that have accelerated Dune Security’s trajectory. Strategic alliances have extended our reach and impact from the earliest stages, and this milestone was achieved through one such collaboration: “We place immense value on the alliances we have built at Dune Security. In this case, we were able to leverage a great alliance with our banking partner, Rho, whose support helped make this moment possible,” said DellaPelle.
Partnerships like this reflect the foundation of trust at scale – where strong alliances fuel momentum, accelerate growth, and enable us to deliver on our mission with greater reach and impact. The trust we have in our people and partners, and the urgency we bring to preventing social engineering and insider threats, continue to drive us forward.
“To be here in Times Square is incredible. We can look up and see the names of our customers on these buildings, and to know we’re helping them solve such a challenging and persuasive problem is hard to put into words,” Waite added.

Key Takeaways
Featured Speakers
Never Miss a Human Risk Insights
Subscribe to the Dune Risk Brief - weekly trends, threat models,and strategies for enterprise CISOs.
FAQs

Seeing our mission to stop insider threats and social engineering lit up on a six-story billboard in Times Square is a rare milestone for any seed-stage company. It reflects the urgency of the threats we’re solving, the strength of our partnerships, and the pride we have in the team driving our growth.

Dune Security goes beyond compliance and generic training by comprehensively quantifying and individually reducing user risk. Our platform scores user risk, simulates real-world attacks, and adapts remediation in real time to deliver the visibility and resilience legacy defenses cannot provide. We identify the users most at risk and enable security teams to act proactively before a breach occurs.

90% of breaches still start with human behavior. Attackers exploit people, not firewalls, and every compromised click or manipulated decision can escalate into enterprise-wide exposure. By measuring and reducing user risk in real time, Dune Security equips organizations with stronger protection today and builds lasting resilience against tomorrow’s attacks.

Social engineering and insider threats are especially dangerous today because attackers use AI and manipulation to bypass traditional defenses. They exploit trust through impersonation, account takeover, and real-time pressure, turning ordinary users into unknowing insiders. Only visibility and control at the user layer can stop these risks and build lasting resilience.

It reflects the ambition and urgency that define our team. From a serendipitous meeting at JFK to Times Square, we’ve built a culture where every person contributes directly to solving one of cybersecurity’s hardest problems. Collaboration, trust, and relentless execution drive us forward, and this milestone is proof of what that culture can achieve.




The Top User-Driven Cyber Threats Targeting Law Firms
Law firms sit on some of the most sensitive and valuable data in the enterprise, and attackers have built an entire playbook around exploiting the users who handle it. Learn how four dominant threat vectors are targeting legal sector workflows in 2026 and what it takes to stop attacks at the User Layer.




The Workforce Has Expanded: How Attackers Are Targeting Enterprise AI Agents
AI agents are being deployed across the enterprise at scale, and attackers have already started engineering against them. Learn how agentic AI expands the enterprise attack surface in ways legacy security programs were never designed to defend.
.avif)
.avif)


Making Cyber Risk Board Ready: Strategies for Winning Boardroom Confidence
Winning board confidence on cyber risk requires more than technical reporting. Security leaders need to support better governance decisions and communicate exposure in a way directors can act on.